Prompt Injection Attacks Against LLM Agents: The Complete Technical Guide for 2026
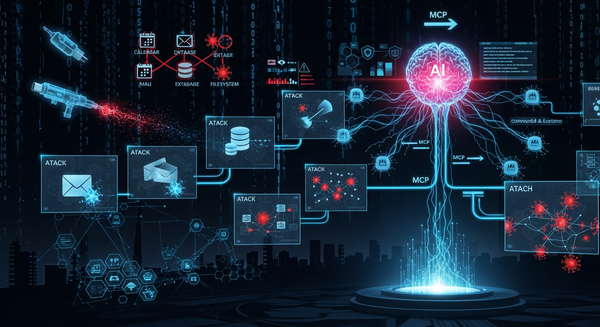
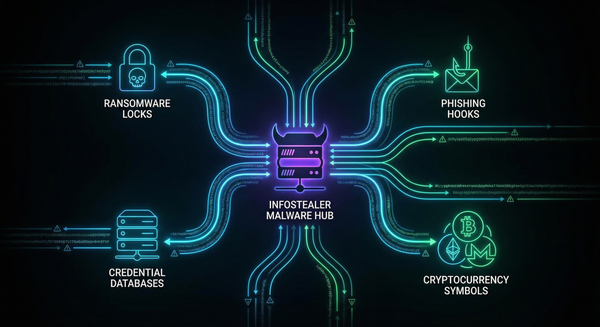
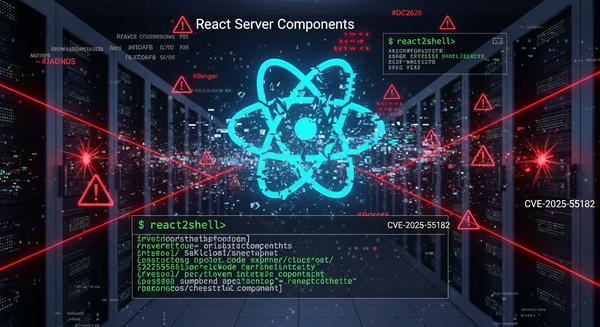
When AI Can Execute Code, Every Injection Is an RCE A comprehensive technical analysis of prompt injection vulnerabilities in agentic AI systems, with real-world CVE breakdowns, attack taxonomies, and practical defense strategies TL;DR Prompt injection isn't just about making ChatGPT say naughty words. When LLM agents have