Tutorial: Assessing Insecure Ports for Vulnerabilities
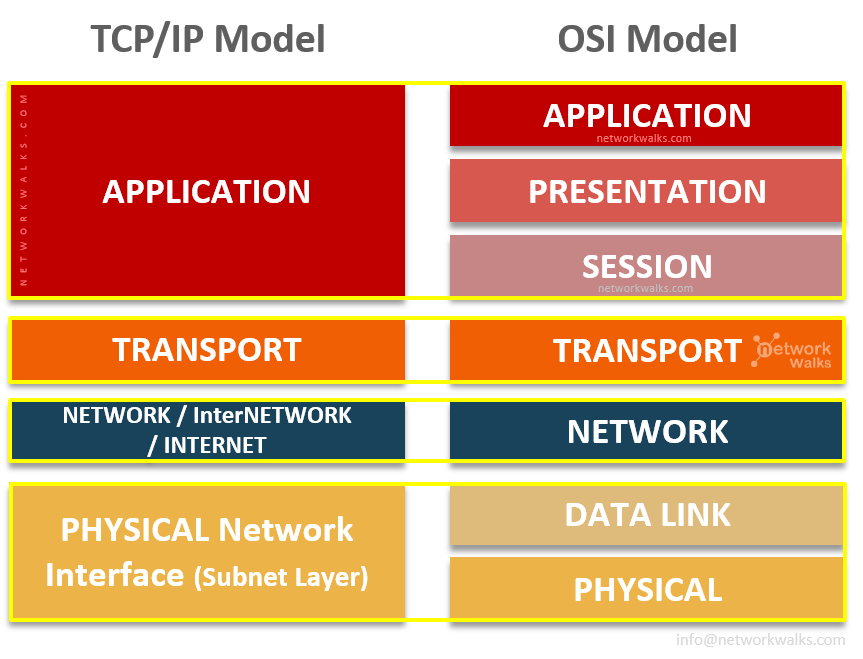
1. Introduction Network ports are entry points through which data flows between a computer and the internet or other devices on a network. Some ports are inherently insecure due to the nature of the protocols they use. Assessing these insecure ports is crucial for understanding potential vulnerabilities that attackers might