RondoDox Botnet: From Pwn2Own Exploits to Global Infrastructure Attacks
Executive Summary
A sophisticated botnet campaign dubbed RondoDox has emerged as one of 2025's most alarming cybersecurity threats, targeting internet-exposed infrastructure across the globe. Using an "exploit shotgun" approach, RondoDox weaponizes over 56 vulnerabilities spanning more than 30 vendors, including high-profile flaws first demonstrated at prestigious Pwn2Own hacking competitions. This large-scale campaign represents a dangerous evolution in automated exploitation, putting millions of routers, DVRs, NVRs, CCTV systems, and other network devices at risk.
According to Trend Micro's Zero Day Initiative (ZDI) and research teams, the campaign has been actively exploiting devices since mid-2025, with several targeted CVEs now included in CISA's Known Exploited Vulnerabilities (KEV) catalog. Organizations with internet-facing network infrastructure face immediate risks of data exfiltration, persistent network compromise, and operational disruption.
The Pwn2Own Connection: When Security Research Becomes Weaponized
What is Pwn2Own?
Before diving into RondoDox, it's crucial to understand the Pwn2Own connection. Pwn2Own is one of the world's most prestigious hacking competitions, first held in April 2007 at the CanSecWest security conference in Vancouver. The contest, now organized by Trend Micro's Zero Day Initiative, challenges elite security researchers to exploit widely-used software and devices with previously unknown vulnerabilities.
Winners receive the hacked device plus substantial cash prizes—recent competitions have awarded over $1 million per event. The name "Pwn2Own" derives from contestants needing to "pwn" (hack) the device to "own" (win) it.
From White Hat to Black Hat
The first RondoDox intrusion detected by Trend Micro on June 15, 2025, exploited CVE-2023-1389—a vulnerability targeting the WAN interface of the TP-Link Archer AX21 Wi-Fi router. This specific flaw was originally demonstrated at Pwn2Own Toronto 2022 by researchers Tri Dang and Bien Pham from Qrious Secure, who successfully chained together an authentication bypass and command injection vulnerability.
This represents a disturbing trend: vulnerabilities responsibly disclosed through competitions like Pwn2Own are being rapidly weaponized by botnet operators. The window between public disclosure and widespread exploitation continues to shrink, even when vendors issue patches promptly.
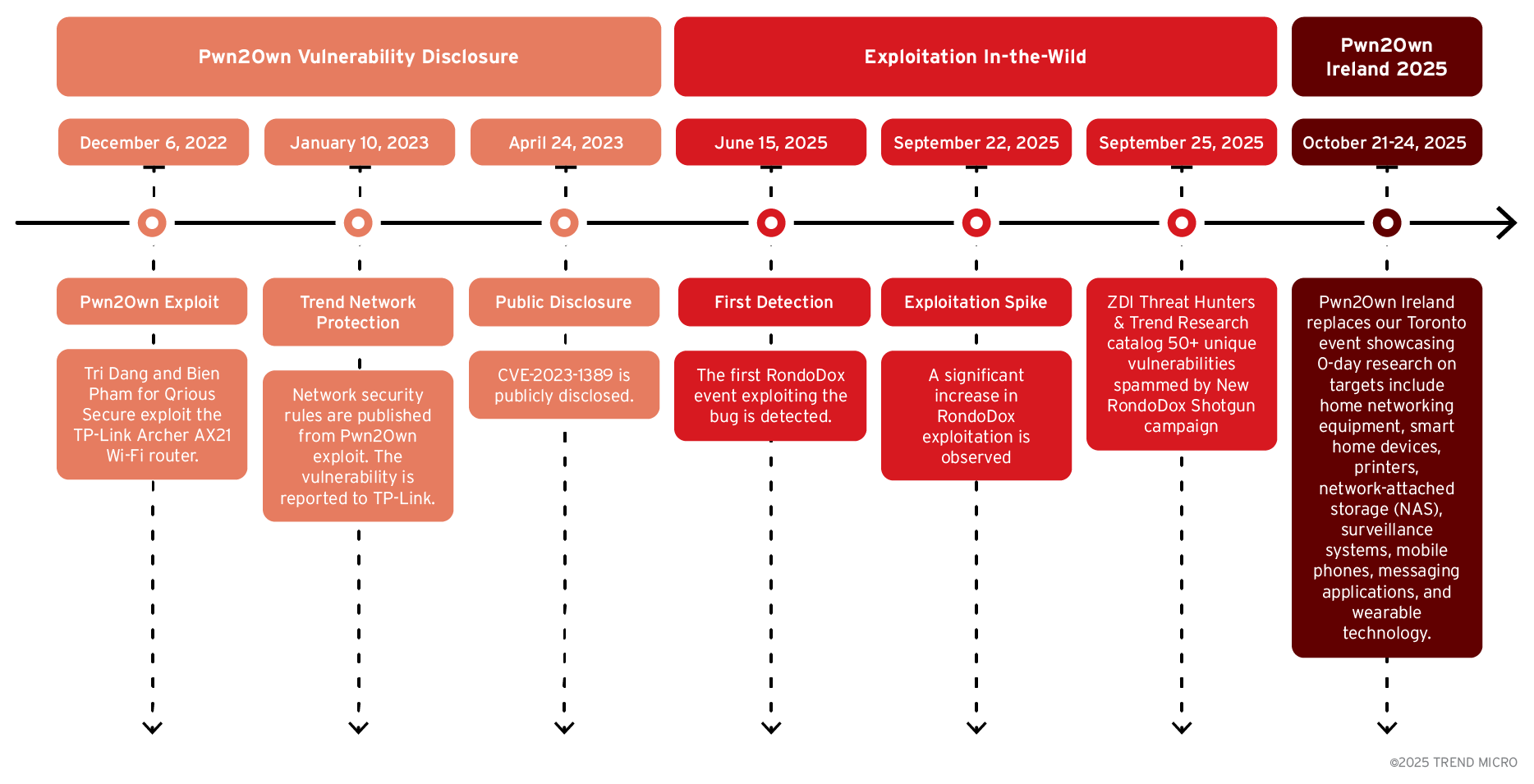
Timeline: From Discovery to Exploitation
- December 6, 2022: Vulnerability demonstrated at Pwn2Own Toronto 2022
- January 10, 2023: Trend Network Security publishes detection rule
- January 15, 2023: Coordinated disclosure of CVE-2023-1389 to TP-Link
- June 15, 2025: First RondoDox exploitation detected using this vulnerability
- September 22, 2025: Massive exploitation spike observed in Trend telemetry
- September 25, 2025: CloudSEK reports 230% attack surge with loader-as-a-service model
RondoDox Background: A New Botnet Emerges
RondoDox first surfaced publicly in mid-2025 as documented by FortiGuard Labs, initially focusing on TBK DVRs and Four-Faith routers through exploitation of CVE-2024-3721 and CVE-2024-12856. The botnet distinguishes itself from older variants like Mirai or Gafgyt through several sophisticated characteristics:
Advanced Evasion Techniques
- Custom libraries built to avoid common detection signatures
- Traffic mimicry disguising command-and-control communications as gaming platform or VPN server traffic
- Anti-analysis measures including process termination of debugging tools
- XOR-encoded configuration data to obscure payloads
- Multi-architecture payloads targeting ARM, MIPS, Intel 80386, MC68000, PowerPC, SuperH, ARCompact, x86-64, and AArch64
Persistence Mechanisms
RondoDox employs layered persistence strategies to survive device reboots and remediation attempts:
- Init script modification: Appends launch commands to
/etc/rcS,/etc/init.d/rcS, and/etc/inittab - Crontab injection: Adds entries to both user and root crontab schedules
- Signal handling: Instructs infected hosts to ignore SIGINT, SIGQUIT, and SIGTERM termination signals
- Self-healing routines: Periodically reinstalls components if removed
Upon execution, RondoDox scans for and terminates specific applications including network utilities (wget, curl), system analysis tools (Wireshark, gdb), and competing malware (cryptominers, Redtail variants).
The Exploit Shotgun: RondoDox's Expanded Arsenal
The term "exploit shotgun" perfectly describes RondoDox's strategy—instead of targeting specific vulnerabilities with precision, it fires a barrage of exploits simultaneously to maximize infection rates. This approach prioritizes volume over stealth, creating massive attack surfaces across vulnerable infrastructure.
Vulnerability Breakdown
Total Targeted Flaws: 56
- CVE Assigned: 38 vulnerabilities
- No CVE Assigned: 18 vulnerabilities (zero-days or unreported flaws)
By Vulnerability Type:
- Command Injection (CWE-78): 50 exploits
- Path Traversal (CWE-22): 2 exploits
- Buffer Overflow (CWE-120): 1 exploit
- Authentication Bypass (CWE-287): 1 exploit
- Memory Corruption (CWE-119): 1 exploit
Notable Exploited Vulnerabilities
High-Profile CVEs in CISA KEV Catalog:
TP-Link Archer AX21 (CVE-2023-1389)
- Pwn2Own Toronto 2022 demonstration
- Command injection in locale controller
- Targets WAN interface
TBK DVRs (CVE-2024-3721)
- Critical command injection in
/device.rspendpoint - Affects DVR-4104 and DVR-4216 models
- mdb and mdc parameters exploitable
Four-Faith Industrial Routers (CVE-2024-12856)
- Authenticated remote command execution
- Exploits
apply.cgiinterface - Affects F3x24 and F3x36 models
Apache HTTP Server (CVE-2021-41773 & CVE-2021-42013)
- Path traversal enabling remote code execution
- Affects improperly configured instances
GNU Bash "Shellshock" (CVE-2014-6271)
- Over a decade old, still widely exploitable
- Remote code execution through environment variables
- Affects legacy systems and IoT devices
Vendors Targeted:
Network Equipment:
- D-Link (multiple router and NAS models)
- Netgear (R7000, R6400, DGN1000, multiple others)
- TP-Link (Archer AX21, TL-WR840N)
- Linksys (E-Series routers, multiple variants)
- TOTOLINK (multiple router models)
- Tenda (multiple router models)
- ZyXEL (P660HN-T1A)
- Cisco (RV110W, RV130W, RV215W)
- LB-LINK (multiple routers)
- Edimax (RE11S Router)
Surveillance & DVR Systems:
- TBK (DVR-4104, DVR-4216)
- LILIN DVRs
- TVT NVMS-9000 DVRs
- Digiever DS-2105 Pro
- QNAP VioStor NVR
- AVTECH CCTV systems
- Brickcom IP cameras
Other Devices:
- Four-Faith Industrial Routers
- Fiberhome Routers
- ASMAX 804 Router
- IQrouter 3.3.1
- Ricon Industrial Cellular Router
- Belkin Play N750
- Meteobridge Web Interface
Zero-Day and Unreported Vulnerabilities
Particularly concerning is RondoDox's exploitation of 18 command injection flaws without assigned CVE identifiers. These include vulnerabilities in:
- D-Link DNS-343 ShareCenter / goAhead Web Server
- Various endpoints across multiple vendors (wlan_operate, resize_ext2, shell)
- File upload mechanisms
- Unknown devices with vulnerable interfaces
The presence of these unreported flaws suggests either zero-day exploitation or long-standing vulnerabilities in discontinued or poorly-maintained products.
The Loader-as-a-Service Model
By September 2025, RondoDox evolved to leverage a loader-as-a-service (LaaS) infrastructure, significantly amplifying its threat profile. CloudSEK's analysis revealed that this operation co-packages RondoDox with Mirai and Morte payloads, creating a multi-threat delivery system.
Key Characteristics of the LaaS Operation:
Rapid Infrastructure Rotation
- Constant IP and domain cycling to evade blocklists
- Distributed command-and-control servers across multiple jurisdictions
- Exposed C2 logs initially provided six months of attack data before operators secured systems
230% Attack Surge
- Between July and August 2025, attacks spiked dramatically
- Multi-architecture malware deployment
- Targeted both SOHO routers and enterprise applications
Attack Vectors
- Exploitation of unsanitized POST parameters (NTP, syslog, hostname fields)
- Default credential abuse across thousands of device types
- Command injection through web interfaces
- Weak authentication bypasses
Post-Exploitation Activities
Once devices are compromised, RondoDox operators leverage infected infrastructure for:
- DDoS-for-Hire Services: Enrolling devices in distributed denial-of-service botnets
- Cryptocurrency Mining: Deploying cryptomining payloads on infected systems
- Proxy Networks: Using compromised devices as stealth proxies for additional attacks
- Enterprise Infiltration: Pivoting from IoT devices into corporate networks
- Data Exfiltration: Stealing sensitive information from surveillance systems and network devices
The operators have been linked to email addresses including bang2012@protonmail.com and makenoise@tutanota.de, which appear in numerous exploitation samples.
Global Impact and Scale
Geographic Distribution
Active exploitation has been observed globally since mid-2025, with traffic originating from:
- Brazil
- Argentina
- Iran
- China
- Mexico
- Russia
- South Africa
- Ecuador
- And numerous other countries
At-Risk Organizations
Particularly Vulnerable Sectors:
Small and Medium Businesses (SMBs)
- Often maintain internet-exposed devices with default configurations
- Limited cybersecurity budgets and staffing
- Surveillance systems in retail stores, restaurants, warehouses
Critical Infrastructure
- Industrial control systems
- HVAC and building management systems
- Physical security systems
Healthcare Facilities
- Medical imaging devices
- Facility surveillance systems
- Network-connected medical equipment
Educational Institutions
- Campus surveillance systems
- Building access controls
- Legacy network infrastructure
Government Facilities
- Public infrastructure monitoring
- Security camera networks
- Emergency services systems
The End-of-Life Device Problem
A significant challenge lies in the exploitation of end-of-life (EoL) devices no longer receiving security updates from manufacturers. RondoDox heavily targets these abandoned devices, including:
- D-Link routers from 2015 and earlier
- Belkin devices from 2014
- Legacy Cisco equipment
- Discontinued DVR and NVR systems
Organizations continuing to operate these devices face impossible security challenges—vendors will not patch the vulnerabilities, yet the devices remain valuable attack vectors.
Protection Strategies: Defending Against RondoDox
Immediate Actions
1. Patch Management Priority
- Apply all available firmware updates for internet-facing devices immediately
- Prioritize CVEs listed in CISA's KEV catalog
- Subscribe to vendor security advisories
2. Replace End-of-Life Equipment
- Identify and inventory all EoL devices on your network
- Budget for replacement of devices no longer receiving security updates
- Avoid purchasing used or legacy equipment
3. Change Default Credentials
- Never use factory default usernames and passwords
- Implement strong, unique passwords for every device
- Use a password manager to track credentials
4. Disable Unnecessary Services
- Turn off unused remote access features (Telnet, SSH, HTTP management)
- Disable UPnP if not required
- Close unnecessary network ports
Network Architecture Best Practices
Network Segmentation
Implement strict network segmentation to isolate IoT devices:
Corporate Network (VLAN 10)
└── Workstations, servers, critical systems
IoT Network (VLAN 20)
└── Surveillance cameras, DVRs, NVRs
Guest Network (VLAN 30)
└── Visitor devices, temporary access
DMZ (VLAN 40)
└── Internet-facing services
Benefits:
- Limits lateral movement if one device is compromised
- Enables targeted monitoring of IoT device behavior
- Facilitates granular firewall rule implementation
- Contains breach radius
Firewall Configuration
- Deny all inbound traffic to IoT devices from the internet by default
- Allow only required outbound connections (e.g., firmware update servers)
- Implement stateful inspection to detect anomalous traffic patterns
- Block traffic between IoT VLAN and corporate network except through authorized gateways
Monitoring and Detection
Implement Continuous Monitoring
Deploy intrusion detection systems (IDS) tailored for IoT:
- Monitor for unusual outbound connections
- Detect command injection patterns in HTTP traffic
- Flag suspicious process execution on Linux-based devices
- Track firmware modification attempts
Key Indicators of Compromise (IoCs)
Watch for these RondoDox-specific indicators:
Process Commands:
- "#!/bin/sh" && "chmod 777" && "service apparmor stop" && "rondo."
Email Addresses in Configuration:
- bang2012@protonmail.com
- makenoise@tutanota.de
- vanillabotnet@protonmail.com
Network Behavior:
- Connections to known C2 infrastructure
- Traffic patterns mimicking gaming or VPN services
- Rapid scanning of specific ports (23, 22, 80, 8080)
YARA Rules for Detection
Trend Micro has provided detection rules for RondoDox:
rule ZTH_Malware_RondoDox_Loader_A {
meta:
description = "Detects RondoDox post exploitation"
date = "2025-09-29"
strings:
$s0 = "#!/bin/sh" ascii
$s1 = "chmod 777" ascii
$s2 = "service apparmor stop" ascii
$r1 = /\brondo\./ nocase
condition:
all of them
}
Advanced Security Measures
Zero Trust Architecture
Implement Zero Trust principles for IoT:
- Verify every device before granting network access
- Use certificate-based authentication where possible
- Implement micro-segmentation at the device level
- Continuously validate device identity and posture
Encrypted Communications
- Enforce TLS 1.3 or higher for all device communications
- Use WPA3 for wireless networks
- Deploy VPN tunnels for remote device management
- Avoid unencrypted protocols (HTTP, Telnet, FTP)
Device Lifecycle Management
- Maintain comprehensive asset inventory of all IoT devices
- Track firmware versions and vulnerability status
- Automate firmware update deployment where possible
- Plan device refresh cycles to avoid EoL issues
Physical Security
- Secure physical access to network equipment
- Use tamper-evident seals on critical devices
- Monitor for unauthorized physical access attempts
- Implement video surveillance of equipment rooms
Vendor-Specific Protections
Trend Micro Solutions
Organizations using Trend Micro products have protection through:
Network Security Rules:
- 46070 - HTTP: TBK DVR Command Injection Vulnerability
- 42150 - HTTP: TP-Link AX1800 locale controller Command Injection (CVE-2023-1389)
- 45300 - HTTP: Four-Faith Industrial Router Command Injection
- 40064 - HTTP: D-Link Various Routers Remote Code Execution
- And 60+ additional detection rules
Endpoint Protection:
- VSAPI detection patterns for Mirai variants
- Backdoor.Linux.* family detections
- Trojan.Linux.* family detections
Vision One Platform:
- Centralized threat intelligence
- IOC sweeping capabilities
- Hunting queries for RondoDox indicators
- Integrated network and endpoint visibility
General Security Vendors
Most enterprise security solutions can detect RondoDox through:
- Signature-based detection of known payloads
- Behavioral analysis of command execution patterns
- Network traffic anomaly detection
- File integrity monitoring for modified init scripts
Lessons Learned: The Vulnerability Lifecycle Problem
The RondoDox campaign exposes uncomfortable truths about modern cybersecurity:
1. The Disclosure-to-Exploitation Window is Shrinking
Even when researchers responsibly disclose vulnerabilities through programs like Pwn2Own and vendors promptly issue patches, the time window before active exploitation is measured in months—or even weeks. Organizations that delay patching create opportunities for campaigns like RondoDox.
2. IoT Security Remains an Afterthought
Many IoT devices are deployed with:
- Minimal security testing
- No secure update mechanisms
- Poor credential management
- Limited vendor support lifecycles
Consumers and businesses often purchase these devices without considering long-term security implications.
3. End-of-Life Devices Pose Ongoing Risks
Devices reaching end-of-life but remaining deployed create permanent vulnerabilities. Organizations must plan for device replacement cycles and actively decommission unsupported equipment.
4. Awareness Gaps Persist
Many small businesses and home users remain unaware that their routers, cameras, and smart devices require regular updates and security attention. This creates massive pools of vulnerable devices for botnet recruitment.
Looking Forward: The Future of IoT Botnets
RondoDox represents an evolution in botnet sophistication, but it won't be the last of its kind. Several trends will shape future IoT security challenges:
Increasing Automation
- AI-assisted vulnerability discovery and exploitation
- Automated exploit chain development
- Machine learning-powered evasion techniques
Expanded Attack Surfaces
- 5G connectivity enabling more IoT deployments
- Edge computing introducing new vulnerable platforms
- Software-defined vehicles becoming attack targets
- Smart city infrastructure providing large-scale targets
Regulatory Responses
Governments worldwide are responding with new IoT security regulations:
- EU Cyber Resilience Act: Mandating security requirements for connected devices
- US IoT Cybersecurity Improvement Act: Setting baseline security standards
- UK Product Security and Telecommunications Infrastructure Act: Requiring security by design
These regulations will force manufacturers to improve device security, but enforcement and adoption will take years.
Conclusion: Acting Now to Prevent Future Compromise
The RondoDox botnet campaign serves as a stark reminder that IoT security cannot be an afterthought. Organizations maintaining internet-exposed network infrastructure face real and immediate threats from automated exploitation campaigns targeting known vulnerabilities.
Key Takeaways:
- Patch immediately: Prioritize firmware updates for all internet-facing devices, especially those in CISA's KEV catalog
- Inventory your exposure: Many organizations don't know what IoT devices exist on their networks—conduct comprehensive asset discovery
- Segment networks: Isolate IoT devices from critical systems to limit breach impact
- Replace EoL equipment: Devices without vendor support should be retired and replaced
- Monitor continuously: Implement detection capabilities for IoT-specific threats
- Plan for lifecycle management: Build device refresh cycles into budgets to avoid accumulating vulnerable infrastructure
- Educate users: Ensure staff understand IoT security risks and best practices
The uncomfortable reality is that the vulnerabilities exploited by RondoDox have been public knowledge for months or years. The campaign succeeds not through sophistication but through exploiting organizations' failure to apply basic security hygiene.
As we await the next Pwn2Own Ireland 2025 event, we must recognize that the valuable security research conducted at these competitions can quickly become weaponized if organizations don't act swiftly to patch disclosed vulnerabilities. The race between defenders and attackers continues to accelerate—and in that race, delay equals defeat.
Your network devices are either patched or they're recruitment targets for the next botnet. The choice is yours.
Additional Resources
CISA KEV Catalog: https://www.cisa.gov/known-exploited-vulnerabilities-catalog
Trend Micro RondoDox Analysis: https://www.trendmicro.com/en_us/research/25/j/rondodox.html
Pwn2Own Event Information: https://www.zerodayinitiative.com/
FortiGuard Labs RondoDox Report: https://www.fortinet.com/blog/threat-research/rondobox-unveiled-breaking-down-a-botnet-threat
CloudSEK Loader Analysis: https://www.cloudsek.com/blog/botnet-loader-as-a-service-infrastructure-distributing-rondodox-and-mirai-payloads
This article is based on research published by Trend Micro's Zero Day Initiative, FortiGuard Labs, CloudSEK, and additional cybersecurity sources. All technical details have been verified through multiple authoritative sources.
Published on hackernoob.tips | Stay informed. Stay secure.





