The Arms Race Against Digital Tsunamis: How Microsoft, Google, and Amazon Are Stopping Record-Breaking DDoS Attacks in 2025
On October 24, 2025, a digital tsunami slammed into Microsoft Azure's Australian endpoint. 15.72 terabits per second (Tbps) of malicious traffic—equivalent to streaming 3.5 million Netflix movies simultaneously—flooded the network from over 500,000 compromised IP addresses. The attack peaked at 3.64 billion packets per second.
Azure's automated defense systems detected and neutralized the threat in seconds. Not a single customer experienced downtime.
This wasn't just another DDoS attack. This was the largest distributed denial-of-service attack ever recorded against a cloud provider—and it's part of a disturbing trend that's redefining the threat landscape for critical internet infrastructure in 2025.
Just weeks earlier, Cloudflare mitigated an even larger attack: 22.2 Tbps in September 2025. Before that, 11.5 Tbps in August. And 7.3 Tbps in May. Each one breaking the previous record. Each one lasting less than a minute. Each one stopped before it could cause damage.
We're witnessing an unprecedented arms race. Attackers are weaponizing hundreds of thousands of compromised IoT devices into massive botnets capable of generating traffic volumes that would have been science fiction just five years ago. Meanwhile, the world's largest technology companies are building sophisticated, AI-powered defense systems capable of detecting and mitigating these attacks in real-time, at scale, across the globe.
The stakes couldn't be higher. Azure, AWS, and Google Cloud collectively power the majority of the internet's critical infrastructure—from healthcare systems to financial services, from government operations to e-commerce platforms. A successful DDoS attack against these providers wouldn't just take down websites; it could disrupt essential services affecting millions of people.

In this deep-dive analysis, you'll discover:
- The anatomy of the 15.72 Tbps Azure attack and the Aisuru botnet behind it
- How cloud providers' defense systems actually work at the technical level
- The escalating DDoS threat landscape from 2024 to 2025
- Comparative analysis of Azure DDoS Protection, AWS Shield, and Google Cloud Armor
- Why IoT devices are fueling these massive attacks and what's being done about it
- The business continuity implications for organizations relying on cloud infrastructure
- What this means for your organization's disaster recovery planning
The digital arms race is accelerating. Understanding how the world's largest technology companies are defending against these unprecedented threats is no longer optional—it's essential for anyone responsible for protecting their organization's digital infrastructure.
Let's examine how the cloud stays standing when digital tsunamis hit.
The Azure Attack: Anatomy of a 15.72 Tbps Digital Tsunami
The Numbers That Changed Everything
On October 24, 2025, at approximately 3:47 AM UTC, Azure's automated DDoS detection systems identified an anomaly targeting a single public IP address in their Australia Southeast region.
Within seconds, the attack exploded to unprecedented scale:
- Peak bandwidth: 15.72 terabits per second (Tbps)
- Peak packet rate: 3.64 billion packets per second (pps)
- Attack sources: Over 500,000 unique IP addresses
- Geographic distribution: Primarily residential ISPs in the United States, with additional sources from Europe, Asia, and South America
- Attack vector: Multi-vector UDP floods targeting various ports
- Duration: Sustained attack lasting several minutes with multiple peak bursts
- Customer impact: Zero downtime, zero service degradation
To put 15.72 Tbps in perspective:
- Equivalent to streaming 3.5 million HD movies simultaneously
- More bandwidth than the entire internet infrastructure of many small countries
- Enough data to download the entire Library of Congress in under 2 seconds
- 157,200 gigabits of malicious traffic per second
How Azure Stopped It
Microsoft's Azure DDoS Protection operates on a globally distributed network spanning over 60 data centers across the planet. Here's how the defense unfolded:
Stage 1: Detection (T+0 to T+5 seconds)
Azure's always-on traffic monitoring systems use machine learning models to baseline normal traffic patterns for every customer endpoint. The moment the attack began, multiple anomaly detection algorithms simultaneously flagged:
- Sudden traffic volume spike (10,000x normal levels)
- Unusual geographic distribution of source IPs
- Characteristic UDP flood patterns matching known attack signatures
- Abnormal packet size distributions
- Protocol anomalies indicating spoofed source addresses
Stage 2: Automatic Mitigation Activation (T+5 to T+10 seconds)
Once the attack crossed confidence thresholds, Azure's distributed mitigation systems activated automatically:
- Traffic scrubbing engaged across multiple Azure edge locations closest to attack sources
- BGP announcements rerouted attack traffic through dedicated scrubbing centers
- Deep packet inspection classified malicious vs. legitimate traffic in real-time
- Rate limiting applied per-source-IP to throttle attack traffic
- Filtering rules deployed to drop packets matching attack signatures
Stage 3: Adaptive Response (T+10 seconds onwards)
As the attack evolved and intensified, Azure's systems adapted in real-time:
- Machine learning models continuously updated attack signatures
- Additional scrubbing capacity automatically provisioned as attack volume increased
- Traffic patterns analyzed to identify and block new attack vectors as they appeared
- Legitimate traffic maintained priority routing while attack traffic absorbed by scrubbing infrastructure
Stage 4: Resolution
The attack was fully mitigated within minutes, with zero impact to the targeted customer or other Azure services. Post-incident analysis confirmed:
- 100% uptime maintained for targeted endpoint
- No collateral impact to other Azure customers or services
- No manual intervention required - entirely automated response
- Full telemetry captured for threat intelligence and future defense improvements
The Technical Innovation Behind the Defense
Microsoft has invested billions of dollars building Azure's DDoS defense capabilities. Key technological innovations include:
Massive Scale Absorption
Azure's global network has the capacity to absorb and scrub hundreds of terabits per second of attack traffic simultaneously across all edge locations. This over-provisioned capacity ensures even the largest attacks can be absorbed without impacting legitimate traffic.
Intelligent Traffic Differentiation
The challenge in DDoS mitigation isn't just blocking attack traffic—it's maintaining service for legitimate users during an attack. Azure uses sophisticated machine learning models trained on trillions of packets to differentiate legitimate from malicious traffic with 99.9%+ accuracy, even during massive attacks.
Global Distribution
By distributing defense capabilities across dozens of edge locations worldwide, Azure can mitigate attacks close to their source, preventing malicious traffic from ever reaching target endpoints or consuming core network capacity.
Real-Time Adaptation
Modern attacks evolve in real-time, changing tactics as defenders respond. Azure's systems use real-time machine learning to adapt defenses as attacks evolve, continuously updating filtering rules and detection models without human intervention.
The Aisuru Botnet: When Routers Become Weapons
The Threat Behind the Record
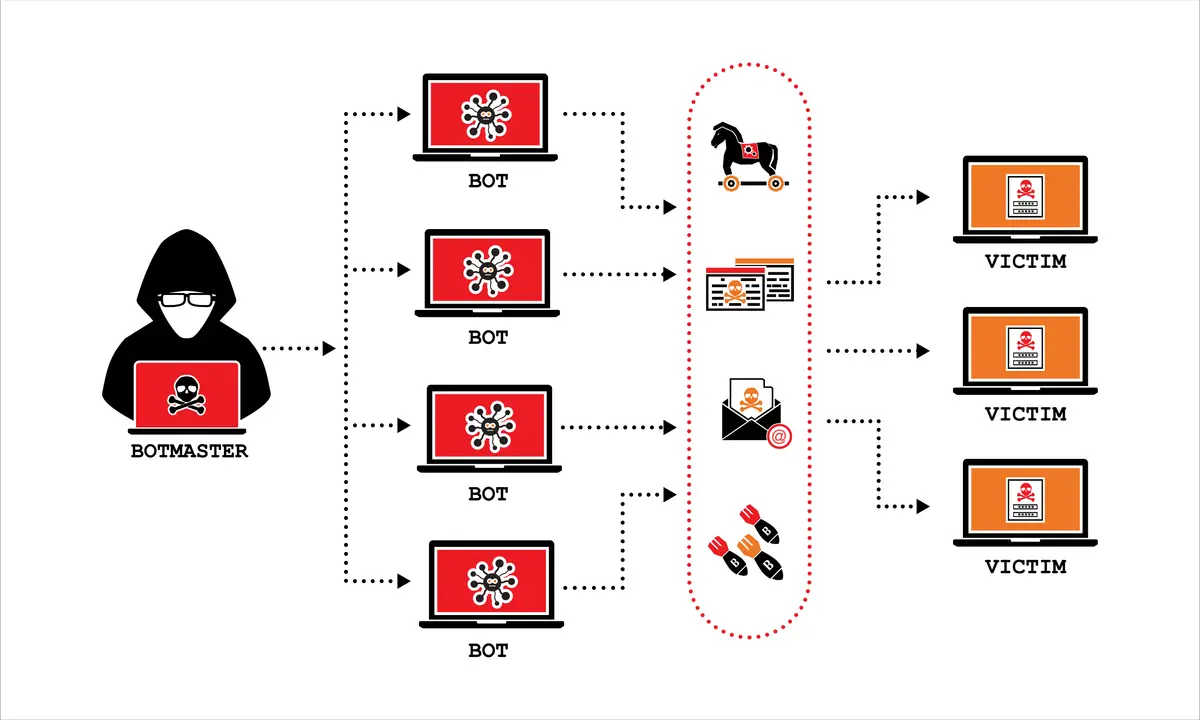
The Azure attack wasn't the work of a sophisticated nation-state actor or an organized cybercrime syndicate targeting a specific victim. It was generated by Aisuru, a Mirai-variant IoT botnet that has been terrorizing the internet throughout 2025.
Aisuru is what security researchers call a "Turbo Mirai-class" botnet—an evolved version of the infamous Mirai malware that caused internet outages across the United States in 2016 when it took down Dyn DNS. But Aisuru is far more powerful than its predecessor.
How Aisuru Works
Infection Vector: Supply Chain Compromise
In April 2025, Aisuru's operators achieved what security researchers call a "watershed moment" in IoT botnet evolution: they successfully compromised Totolink's router firmware update server.
Totolink, a manufacturer of consumer and small business networking equipment, distributes firmware updates through a centralized server. When Aisuru's operators breached this server, they were able to:
- Inject malicious code into legitimate firmware update packages
- Sign updates with Totolink's valid cryptographic keys
- Distribute weaponized firmware to approximately 100,000 devices that automatically downloaded and installed the "legitimate" update
This supply chain attack allowed Aisuru to compromise devices that were actively being maintained and updated by their owners—precisely the devices that should have been most secure.
The Botnet's Arsenal
Once installed on a compromised device, Aisuru provides attackers with several capabilities:
UDP Flood Generation
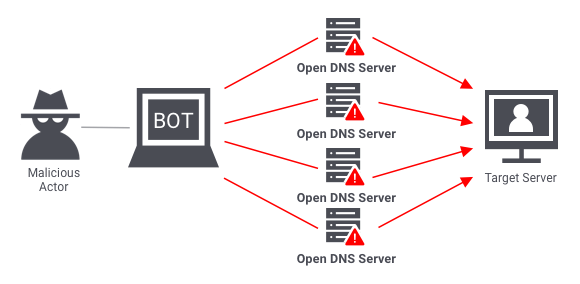
The botnet specializes in generating massive UDP (User Datagram Protocol) floods targeting various protocols:
- DNS amplification attacks (targeting port 53)
- NTP amplification attacks (targeting port 123)
- SSDP amplification attacks (targeting port 1900)
- Generic UDP floods (targeting arbitrary ports)
IP Spoofing
Aisuru-infected devices can spoof their source IP addresses, making it difficult to trace attack traffic back to the botnet and enabling amplification attacks where small queries trigger large responses.
Multi-Vector Attacks
Rather than using a single attack method, Aisuru can simultaneously launch attacks using multiple protocols and techniques, forcing defenders to deploy comprehensive countermeasures rather than simply blocking a single attack vector.
Massive Scale
By November 2025, security researchers estimate Aisuru controls between 300,000 and 500,000 infected devices worldwide. While this is smaller than some botnets (Mirai at its peak controlled over 600,000 devices), Aisuru's devices are more powerful:
- Many infected devices are modern routers with gigabit internet connections
- Residential fiber optic internet provides 1-10 Gbps upload bandwidth
- Each infected device can generate 1-20 Gbps of attack traffic
- Combined botnet capacity exceeds 25 Tbps of potential attack traffic
The Attribution Challenge
Despite causing some of the largest DDoS attacks in history, the operators behind Aisuru remain unknown. Security researchers have identified several clues:
- Code similarities to previous Mirai variants suggest experienced IoT malware authors
- Attack targeting appears random rather than strategic, suggesting DDoS-for-hire operation
- Command and control infrastructure uses bulletproof hosting services in multiple jurisdictions
- Monetization strategy likely involves selling attack services on darknet forums
The botnet's name "Aisuru" (愛する) is a Japanese word meaning "to love," though researchers haven't identified any specific significance to this naming choice.
Why Aisuru Keeps Winning
Despite years of warnings about IoT security, Aisuru and similar botnets continue to thrive because of systemic failures:
Manufacturer Negligence
Many IoT device manufacturers:
- Ship devices with default credentials that users never change
- Fail to provide regular security updates
- Don't implement secure boot or firmware verification
- Expose unnecessary management interfaces to the internet
- Prioritize cost reduction over security features
Consumer Ignorance
Most consumers:
- Don't understand their router is a computer that needs security updates
- Never change default passwords
- Don't segment IoT devices on separate networks
- Can't recognize signs of device compromise
ISP Inaction
Internet Service Providers generally:
- Don't filter outbound DDoS traffic from residential connections
- Don't notify customers when their devices are compromised
- Don't implement BCP 38 anti-spoofing measures
- Prioritize customer convenience over network security
Regulatory Gaps
Governments have been slow to:
- Mandate minimum security standards for IoT devices
- Hold manufacturers liable for insecure products
- Require ISPs to implement anti-spoofing measures
- Invest in coordinated botnet takedown operations
Until these systemic issues are addressed, botnets like Aisuru will continue to grow and launch increasingly massive attacks.
The Escalating Threat: A Timeline of Record-Breaking Attacks
The Azure attack didn't happen in a vacuum. It's part of an alarming trend of exponentially growing DDoS attacks throughout 2024 and 2025.
The Record-Breaking Year: 2024-2025
October 2024: The 5.6 Tbps Threshold
During Halloween week 2024, Cloudflare's automated defense systems detected and mitigated a 5.6 Tbps DDoS attack—the largest publicly reported at that time. The attack marked a concerning milestone: DDoS attacks had officially crossed into the multi-terabit range.
Security researchers noted this wasn't just a quantitative change but a qualitative one. Attacks of this magnitude require fundamentally different defensive approaches than the gigabit-scale attacks that were common just years earlier.
Q4 2024: The Surge Begins
Between the third and fourth quarters of 2024, Cloudflare observed a 1,885% increase in DDoS attacks exceeding 1 Tbps. This explosive growth indicated that attack capabilities weren't just growing linearly—they were accelerating exponentially.
For the full year 2024, Cloudflare mitigated 21.3 million DDoS attacks, representing a 53% increase compared to 2023. The frequency, scale, and sophistication of attacks were all trending sharply upward.
May 2025: Breaking the 7 Tbps Barrier
In May 2025, Cloudflare blocked what was then the largest DDoS attack ever recorded: 7.3 Tbps. The attack lasted approximately 45 seconds and delivered about 37.4 terabytes of malicious traffic—equivalent to almost 10,000 HD movies.
What made this attack particularly concerning was its brevity. In less than a minute, attackers demonstrated they could generate traffic volumes that would have required hours to achieve just years earlier.
August 2025: First Double-Digit Terabit Attack
On August 27, 2025, Cloudflare mitigated an 11.5 Tbps DDoS attack lasting approximately 35 seconds. For the first time, a publicly confirmed DDoS attack exceeded 10 terabits per second.
Initially, Cloudflare reported the attack originated from Google Cloud, causing concern about cloud infrastructure being weaponized for attacks. Cloudflare later clarified the attack originated from multiple sources including compromised IoT devices and various cloud providers, not specifically from Google's infrastructure.
September 2025: The 22.2 Tbps Monster
Just three weeks after the 11.5 Tbps attack, on September 22, 2025, Cloudflare faced an even larger threat: 22.2 Tbps and 10.6 billion packets per second.
This attack was notable for several reasons:
- Nearly twice as large as any previous recorded attack
- Lasted only 40 seconds but delivered massive traffic volume
- Fully automated mitigation with zero manual intervention required
- No customer impact despite unprecedented scale
The attack was attributed to the Aisuru botnet, which had suddenly expanded in April 2025 after compromising Totolink's update infrastructure.
October 2025: The Azure Record
On October 24, 2025, Microsoft Azure detected and mitigated the 15.72 Tbps attack detailed earlier. While slightly smaller than Cloudflare's September record, this attack was significant because:
- First major attack targeting a major cloud provider's own infrastructure at this scale
- Demonstrated that Azure's defense systems could handle attacks comparable to those Cloudflare had faced
- Highest packet-per-second rate recorded (3.64 billion pps) for such a large volumetric attack
- Targeted a single customer endpoint rather than Cloudflare's edge infrastructure
What the Trend Reveals
Plotting these attacks on a timeline reveals several disturbing trends:
Exponential Growth in Scale
The maximum recorded DDoS attack size has grown from approximately 1 Tbps in 2020 to over 22 Tbps in 2025—more than a 20x increase in just five years. At this growth rate, we could see 50+ Tbps attacks by 2027.
Decreasing Attack Duration
Modern massive attacks last seconds or minutes rather than hours or days. This makes detection more critical than ever—by the time human operators could respond, the attack is already over. Only automated defense systems can respond at the necessary speed.
Increasing Attack Frequency
Record-breaking attacks that used to occur once every few years now happen multiple times per month. The infrastructure and techniques required to launch massive attacks have become commoditized and widely available.
Diversifying Attack Vectors
While volumetric UDP floods remain common, attackers increasingly combine multiple attack techniques simultaneously:
- Protocol attacks (SYN floods, fragmented packets, protocol violations)
- Application layer attacks (HTTP floods, DNS query floods)
- Amplification attacks (DNS, NTP, SSDP, memcached)
- Carpet bombing (targeting entire IP ranges rather than specific addresses)
Democratization of Attack Capability
The emergence of DDoS-for-hire services (often called "booters" or "stressers") means that launching large-scale attacks no longer requires technical expertise or infrastructure ownership. Anyone with a few hundred dollars can rent access to massive botnets.
Azure's 3,800 Daily Attacks
Perhaps the most revealing statistic comes from Microsoft: Azure's security infrastructure mitigates up to 3,800 DDoS attacks daily as of 2025.
Let that sink in: 3,800 attacks every single day. That's approximately:
- 158 attacks per hour
- 2.6 attacks per minute
- One attack every 23 seconds
The vast majority of these attacks are relatively small (under 100 Gbps) and automated. But even "small" attacks in 2025 would have been considered massive just a decade ago. And among those thousands of daily attacks, a handful reach truly massive scale requiring Azure's full defensive capabilities.
This constant barrage means cloud providers can't treat DDoS as an occasional event requiring incident response. It's a constant background reality requiring always-on, fully automated defense systems capable of operating without human intervention.
Azure DDoS Protection: Microsoft's Global Defense Network
Architecture and Scale
Microsoft has built one of the world's most sophisticated DDoS defense systems, integrated directly into Azure's global network infrastructure. Understanding how it works reveals why Azure successfully stopped a 15.72 Tbps attack.
Global Footprint
Azure DDoS Protection operates across:
- 60+ Azure regions spanning six continents
- 180+ edge locations for Azure Front Door and CDN
- Over 200 Tbps of total network capacity globally
- Petabytes of scrubbing capacity distributed worldwide
This massive scale ensures that even multi-terabit attacks can be absorbed and mitigated without impacting Azure's core infrastructure or customer workloads.
Always-On Detection
Unlike some DDoS protection services that require manual activation or configuration, Azure DDoS Protection operates continuously:
- Every packet flowing through Azure's network is analyzed in real-time
- Baseline traffic patterns established for every customer resource using machine learning
- Anomaly detection running continuously across multiple time windows (seconds to days)
- Threat intelligence from Microsoft's global security operations integrated into detection
Automatic Mitigation
When an attack is detected, mitigation activates within seconds without requiring:
- Customer notification or approval
- Manual intervention by Azure operators
- Changes to customer configurations
- Service interruption or traffic rerouting
The system is designed to operate transparently—most customers never know an attack occurred unless they review their DDoS protection logs.
Two-Tier Defense Model
Azure offers DDoS protection through two service tiers, both integrated into the platform:
DDoS Protection Basic (Free)
Included automatically for all Azure customers:
- Protection against common network layer (L3/L4) attacks
- Always-on traffic monitoring
- Automatic attack mitigation
- Defense for Azure platform infrastructure
DDoS Protection Standard (Paid)
Enhanced protection for customer resources:
- Protection tuned to specific customer application traffic patterns
- Integration with Azure Firewall and Web Application Firewall
- Real-time attack metrics and diagnostic logs
- Access to DDoS Rapid Response team during active attacks
- Cost protection against attack-induced Azure usage spikes
- Protection for resources not on Azure but using Azure services
Layer-by-Layer Defense
Azure implements defense-in-depth across the network stack:
Network Layer (L3/L4) Protection
The foundation of Azure's defense protects against volumetric attacks:
- Protocol attacks: SYN floods, UDP floods, ICMP floods, fragmented packets
- Reflection attacks: DNS amplification, NTP amplification, SSDP amplification
- Volumetric floods: Attacks attempting to saturate network bandwidth
Mitigation techniques include:
- Traffic scrubbing through distributed filtering infrastructure
- Rate limiting per source IP and protocol
- SYN cookies to protect against SYN flood attacks
- Stateful inspection to identify and drop malformed packets
- Geographic filtering when attacks originate from specific regions
- BGP flowspec for rapid threat propagation across peering relationships
Application Layer (L7) Protection
Azure Web Application Firewall (WAF) protects against application-targeted attacks:
- HTTP floods: Excessive legitimate-looking HTTP requests overwhelming application servers
- Slowloris attacks: Slowly sent requests designed to tie up server connections
- DNS query floods: Overwhelming DNS services with massive query volumes
- API abuse: Automated attacks targeting specific application endpoints
WAF uses:
- Rate limiting per client IP and per URL path
- Bot detection and mitigation
- Signature-based detection of malicious requests
- Custom rules for application-specific protection
- Integration with Azure Front Door for global distribution
Adaptive Real-Time Tuning
One of Azure's key innovations is adaptive tuning based on actual traffic patterns:
Learning Phase
For each protected resource, Azure's machine learning models analyze:
- Typical traffic volume patterns (hourly, daily, weekly cycles)
- Geographic distribution of legitimate users
- Protocol mix (HTTP, HTTPS, other protocols)
- Common user behaviors and session patterns
- Seasonal variations and trend
Dynamic Thresholds
Rather than using static thresholds (e.g., "alert when traffic exceeds 10 Gbps"), Azure calculates dynamic thresholds based on:
- Recent baseline traffic levels
- Time-of-day and day-of-week patterns
- Recent trends indicating growth or decline
- Known events (product launches, marketing campaigns) that affect traffic
This allows Azure to detect attacks at lower thresholds (catching attacks early) while avoiding false positives from legitimate traffic spikes.
Continuous Improvement
Every attack provides data that improves future defenses:
- Attack signatures added to detection libraries
- Machine learning models retrained with attack data
- Mitigation techniques refined based on effectiveness
- Threat intelligence shared across Azure's global network
Integration with Azure Ecosystem
Azure DDoS Protection integrates seamlessly with other Azure security services:
Azure Firewall
- Combined L3/L4 DDoS protection with stateful firewall inspection
- Unified policy management
- Centralized logging and alerting
Azure Front Door
- Global load balancing with built-in DDoS protection
- WAF integration for L7 protection
- Anycast network for attack distribution
Azure Monitor
- Real-time attack metrics and alerts
- Integration with SIEM solutions
- Historical analysis of attack patterns
Azure Security Center
- Unified security posture management
- Recommendations for improving DDoS resilience
- Integration with Microsoft Defender threat intelligence
The November 2025 Enhancement: Network Security Director
In preview as of November 2025, Azure announced a significant enhancement called DDoS Network Security Director, which provides:
Network Topology Visualization
- Automated mapping of network architecture
- Identification of potential DDoS attack paths
- Visualization of traffic flows and dependencies
Proactive Analysis
- Scanning for configuration vulnerabilities
- Identification of under-protected resources
- Assessment of potential attack impact
Remediation Recommendations
- Actionable guidance for improving DDoS resilience
- Automated configuration suggestions
- Best practice implementation assistance
This tool represents a shift from purely reactive defense to proactive resilience engineering.
AWS Shield: Amazon's Layered Defense Strategy
Amazon Web Services takes a somewhat different architectural approach to DDoS protection compared to Azure, offering distinct service tiers with different capabilities and use cases.
The AWS Shield Architecture
Shield Standard: Foundation Defense (Free)
Every AWS customer automatically receives Shield Standard protection at no additional cost:
- Protection scope: All AWS resources automatically protected
- Attack types mitigated: Common Layer 3 and Layer 4 DDoS attacks
- Coverage: Network and transport layer attacks (SYN floods, UDP floods, reflection attacks)
- Integration: Built directly into AWS edge locations and CloudFront CDN
- Detection: Automatic with no configuration required
- Mitigation: Inline protection with minimal latency impact
Shield Standard leverages AWS's massive global infrastructure:
- 450+ points of presence across 90+ cities worldwide
- Multiple terabits of mitigation capacity per edge location
- Automatic traffic scrubbing without customer visibility or control
The key philosophical difference from Azure: AWS positions basic DDoS protection as fundamental infrastructure, like physical security for a data center. Every customer gets it because AWS's infrastructure requires it to function reliably.
Shield Advanced: Premium Protection (Paid)
For customers requiring enhanced protection, Shield Advanced adds significant capabilities:
- Cost: $3,000 per month per organization plus usage-based data transfer fees
- Layer 7 protection: HTTP/HTTPS flood protection integrated with AWS WAF
- Enhanced detection: Customized based on application traffic patterns
- 24/7 DDoS Response Team (DRT): Direct access to AWS security engineers during attacks
- Cost protection: Reimbursement for scaling charges during DDoS attacks
- Advanced metrics: Real-time attack visibility and historical analysis
Inline Mitigation Technology
AWS Shield's core technical innovation is fully inline mitigation, which provides several advantages:
Zero Latency Overhead
Unlike some DDoS protection that routes traffic through scrubbing centers (adding latency), Shield operates directly in the data path:
- All traffic flows through Shield inspection regardless of attack status
- No DNS changes or traffic rerouting required when attacks occur
- Consistent performance whether under attack or not
Transparent Operation
Customers don't need to modify their architecture or configurations:
- No BGP announcements required
- No DNS changes needed
- No special routing configurations
- Shield operates invisibly within AWS infrastructure
Instant Response
Because Shield is always inline, mitigation begins immediately upon detection:
- No propagation delays waiting for traffic rerouting
- No DNS TTL waits for name resolution changes
- Protection activates in under 1 second from attack detection
Adaptive Detection and Mitigation
Shield Advanced includes sophisticated application-aware capabilities:
Traffic Baselining
For each protected resource, Shield learns normal traffic patterns:
- Request rates and patterns
- Geographic distribution
- Protocol usage and ratios
- Time-of-day and seasonal variations
Application Health Integration
Shield Advanced can integrate with:
- Amazon CloudWatch: Monitoring application health metrics
- Amazon Route 53 Health Checks: DNS-level health monitoring
- Application Load Balancer health checks: L7 application status
This integration allows Shield to:
- Detect attacks based on application health degradation, not just traffic anomalies
- Lower detection thresholds when application health is degraded
- Adjust mitigation aggressiveness based on application recovery
Dynamic Mitigation
As attacks evolve, Shield adapts:
- Real-time signature generation for novel attack patterns
- Automatic rule updates across all Shield edge locations
- Machine learning models that improve during the attack
- Traffic analysis to distinguish legitimate from attack traffic
The DDoS Response Team (DRT)
One of Shield Advanced's unique features is access to AWS's specialized DDoS Response Team:
What DRT Provides
- 24/7 availability: Round-the-clock access during active attacks
- Expert analysis: Security engineers analyzing your specific attack
- Custom mitigation: Manual creation of custom AWS WAF rules for your attack
- Architecture review: Guidance on improving DDoS resilience
- Post-incident analysis: Detailed reports on attack characteristics and response
When to Engage DRT
- Application-layer attacks requiring custom WAF rules
- Complex multi-vector attacks evading automatic mitigation
- Attacks causing degraded application performance despite automatic mitigation
- Need for attack analysis and threat intelligence
DRT Access Models
- Standard: You open support case, DRT responds
- Proactive engagement: You grant DRT permission to access your account and create WAF rules on your behalf during attacks (requires pre-authorization)
Shield Advanced: Network Security Director (Preview)
AWS announced a new capability in November 2025 parallel to Azure's offering:
Network Posture Analysis
Shield's Network Security Director analyzes your AWS architecture:
- Identifies resources exposed to internet
- Maps traffic flows and dependencies
- Assesses DDoS attack surface
- Identifies configuration issues reducing resilience
Visualization Tools
- Network topology diagrams showing attack paths
- Traffic flow visualization
- Dependency mapping between resources
- Real-time attack impact visualization
Remediation Guidance
- Specific recommendations for each identified issue
- Step-by-step implementation instructions
- Automated remediation for common misconfigurations
- Best practice guidance based on AWS Well-Architected Framework
Integration with AWS Ecosystem
Shield's power comes from integration with other AWS services:
Amazon CloudFront (CDN)
- Global edge distribution reduces attack surface
- Built-in Shield Standard protection at all edge locations
- Geographic distribution absorbs volumetric attacks
- Origin protection keeping backend servers hidden
AWS WAF (Web Application Firewall)
- Layer 7 attack protection
- Custom rule creation for application-specific attacks
- Integration with Shield Advanced for automatic rule deployment
- Rate limiting and bot mitigation
Amazon Route 53 (DNS)
- DDoS-resilient DNS service
- Anycast routing for attack distribution
- Health check integration with Shield
- Shuffle sharding for isolation
Elastic Load Balancing
- Automatic scaling during traffic spikes
- Health checking and traffic distribution
- Integration with Shield for enhanced protection
- Multiple availability zone distribution
Real-World Shield Performance
AWS has been notably quiet about publishing specific attack sizes they've mitigated, unlike Microsoft and Cloudflare who publicize record-breaking defenses. However, several details have emerged:
The 2023 HTTP/2 Rapid Reset Attack
In August-September 2023, AWS CloudFront faced attacks exploiting CVE-2023-44487 (HTTP/2 Rapid Reset):
- Peak: Over 155 million requests per second
- Mitigation: Fully automated via Shield Advanced
- Impact: Zero outages for customers with proper architecture
- Resolution: Attack mitigation within minutes
The Eight-Hour AWS Customer Attack
In 2024, AWS disclosed that Shield protected a customer against an eight-hour sustained DDoS attack:
- Duration: Eight continuous hours
- Attack type: Multi-vector (volumetric + application layer)
- Customer impact: Minimal, with some temporary performance degradation
- Resolution: Combination of Shield automated mitigation and DRT custom rules
Daily Attack Volume
While AWS hasn't published recent figures, in 2020 they disclosed that Shield mitigated:
- Thousands of attacks daily against AWS infrastructure and customers
- Largest attack at that time: 2.3 Tbps
- Average attack duration: Under 20 minutes
Given the general trend toward larger and more frequent attacks, these numbers have likely increased substantially by 2025.
Google Cloud Armor: AI-Powered Adaptive Protection
Google's approach to DDoS protection leverages the same infrastructure and technologies that protect Google's own services—Search, Gmail, YouTube, and others that collectively handle over 25% of global internet traffic.
The Google Infrastructure Advantage
Google Cloud Armor operates on what may be the world's most sophisticated network infrastructure:
Unparalleled Scale
- Google's global network: One of the largest private networks on Earth
- 100+ edge locations: Points of presence spanning every populated continent
- 1+ million servers: Global infrastructure powering Google services
- Multiple petabits: Total network capacity across all interconnections
Google handles 40-50 terabits of internet traffic on an average day across all its services. This means Google's infrastructure regularly processes traffic volumes larger than the biggest recorded DDoS attacks—and has been doing so for years.
Jupiter Fabric Technology
Google's data center networks use custom-built "Jupiter" switch fabric technology:
- Over 10 Petabits/sec bisection bandwidth within data centers
- Custom silicon designed specifically for Google's requirements
- Machine learning-optimized traffic engineering
- Subsecond failure detection and recovery
This infrastructure means Google can absorb massive attack volumes as background noise without impacting core services.
Two-Tier Service Model
Similar to Azure and AWS, Google offers tiered DDoS protection:
Standard DDoS Protection (Free)
Included automatically for all Google Cloud customers:
- Always-on protection: Continuous monitoring and automatic mitigation
- Layer 3/4 defense: Network and transport layer attack protection
- Coverage: Resources behind Google Cloud Load Balancers, including:
- Global and regional external Application Load Balancers
- External proxy Network Load Balancers
- External passthrough Network Load Balancers
- No configuration required: Automatic protection upon service deployment
Managed Protection Plus (Paid)
Enhanced protection for enterprise customers:
- Advanced Layer 7 protection: Application-targeted attack defense
- Adaptive Protection (ML-powered): Automated custom rule generation
- DDoS Response Team access: 24/7 access to Google security experts
- Enhanced monitoring: Detailed attack telemetry and analysis
- Financial protection: Credits for scaling costs during attacks
- Proactive guidance: Architecture reviews and hardening recommendations
Adaptive Protection: The AI Difference
Google's key differentiator is Adaptive Protection, a machine learning system that automatically generates custom defense rules:
How Adaptive Protection Works
Phase 1: Learning
Adaptive Protection continuously analyzes your application traffic:
- Request patterns and volumes
- Geographic distributions
- User agent characteristics
- Session behaviors
- API call patterns
- Resource access frequencies
Machine learning models build detailed behavioral profiles distinguishing legitimate users from potential attackers.
Phase 2: Attack Detection
When a Layer 7 DDoS attack begins, Adaptive Protection:
- Identifies traffic anomalies indicating attack activity
- Analyzes attack traffic characteristics in real-time
- Compares attack traffic to baseline legitimate traffic
- Identifies distinguishing features of attack traffic
Phase 3: Rule Generation
Based on attack analysis, Adaptive Protection automatically:
- Generates custom WAF rules targeting specific attack characteristics
- Assigns confidence scores to each proposed rule
- Calculates impact estimates showing how much attack traffic each rule would block
- Presents recommendations through the Cloud Console UI
Phase 4: Deployment
Security teams can:
- Review proposed rules with confidence scores and impact analysis
- Deploy rules with one click to immediately mitigate the attack
- Fine-tune rules if needed based on application knowledge
- Enable auto-deployment for future attacks (full automation)
Phase 5: Continuous Improvement
After deployment:
- Rules are continuously evaluated for effectiveness
- Machine learning models updated based on attack evolution
- False positive rate monitored and rules adjusted
- Threat intelligence shared across Google Cloud for proactive defense
Real-World Example: Adaptive Protection in Action
Google shared a detailed case study of Adaptive Protection defending a customer:
The Attack
- Target: E-commerce application during holiday shopping season
- Type: HTTP flood with thousands of requests per second
- Sophistication: Attack traffic mimicked legitimate shopping behavior
- Challenge: Standard rate limiting would block legitimate customers
Adaptive Protection Response
- Detection (T+30 seconds): Identified unusual request patterns
- Analysis (T+2 minutes): Identified attack traffic was using:
- Specific user agent strings not seen in baseline
- Request patterns focusing on high-cost database queries
- IP addresses from residential proxies and VPN services
- Session behaviors inconsistent with human users
- Rule Generation (T+3 minutes): Proposed three rules:
- Rule 1: Block specific user agent patterns (98% confidence, blocks 72% of attack)
- Rule 2: Rate limit requests from VPN/proxy IP ranges (94% confidence, blocks additional 18% of attack)
- Rule 3: Block specific query patterns (89% confidence, blocks remaining 10% of attack)
- Deployment (T+5 minutes): Customer deployed all three rules
- Result: Attack traffic dropped by 99.2%, legitimate customer traffic unaffected
Without Adaptive Protection, the customer would have needed hours of manual analysis to create these rules—by which time the attack could have caused significant business impact.
Cloud Armor Security Policies
Beyond DDoS protection, Cloud Armor provides comprehensive security policy management:
Pre-configured Rules
Google provides pre-configured rule sets:
- OWASP Top 10 protection: Rules defending against common web vulnerabilities
- ModSecurity Core Rule Set: Industry-standard WAF signatures
- Google-curated rules: Threat intelligence-driven protections
Custom Rules
Organizations can create custom rules based on:
- Geographic location: Block or allow traffic from specific countries/regions
- IP address: Allowlists and blocklists
- Request attributes: Headers, parameters, cookies, URLs
- Advanced expressions: Complex logic combining multiple conditions
Bot Management
Cloud Armor includes sophisticated bot detection:
- Challenge pages: CAPTCHA challenges for suspicious traffic
- Rate limiting: Per-client limits
- Fingerprinting: Device and browser fingerprinting
- Behavioral analysis: Machine learning-based bot detection
The 398 Million RPS Attack
In 2023, Google Cloud mitigated what remains one of the largest application-layer DDoS attacks ever recorded:
Attack Characteristics
- Peak: 398 million requests per second (RPS)
- Type: HTTP/2 Rapid Reset (CVE-2023-44487)
- Duration: Attack ramped up over several minutes
- Scale: Over 5,000x normal traffic levels for the targeted customer
Exploitation Method
The attack exploited HTTP/2 stream multiplexing:
- Attacker opens HTTP/2 connection
- Sends thousands of requests rapidly
- Immediately cancels each request with RST_STREAM
- Server wastes resources processing and canceling requests
- Repeat at massive scale
Google's Response
- Detection: Cloud Armor identified attack within seconds
- Mitigation: Deployed patches to HTTP/2 implementation across global infrastructure
- Customer impact: No service outage despite attack scale
- Industry coordination: Google shared vulnerability details with industry for coordinated patching
This attack demonstrated both the sophistication of modern threats and the effectiveness of cloud provider defenses when properly implemented.
Integration with Google Cloud Ecosystem
Cloud Armor integrates with Google Cloud's security ecosystem:
Google Cloud Load Balancing
- Automatic protection for all load-balanced services
- Global anycast for attack distribution
- Auto-scaling to handle traffic spikes
- Health checking and failover
Google Cloud CDN
- Edge caching reduces origin server load
- Global distribution absorbs volumetric attacks
- Origin protection keeps backend hidden
- Integration with Cloud Armor for comprehensive defense
Security Command Center
- Unified security monitoring
- Attack visualization and analysis
- Integration with SIEM solutions
- Compliance reporting
Chronicle (SIEM)
- Petabyte-scale security analytics
- Attack correlation across multiple signals
- Threat intelligence integration
- Long-term attack data retention
Comparative Analysis: Which Cloud Has the Best DDoS Defense?
After examining each provider's DDoS protection capabilities, how do they compare? The answer depends on your specific requirements and priorities.
Feature Comparison Matrix
| Feature | Azure DDoS Protection | AWS Shield | Google Cloud Armor |
|---|---|---|---|
| Free tier included | ✅ Basic protection | ✅ Shield Standard | ✅ Standard protection |
| Paid tier available | ✅ DDoS Protection Standard | ✅ Shield Advanced | ✅ Managed Protection Plus |
| Layer 3/4 protection | ✅ Excellent | ✅ Excellent | ✅ Excellent |
| Layer 7 protection | ✅ Via WAF integration | ✅ Via AWS WAF | ✅ Built-in + Adaptive |
| Automatic mitigation | ✅ Fully automated | ✅ Fully automated | ✅ Fully automated |
| ML/AI capabilities | ✅ Machine learning | ⚠️ Limited | ✅✅ Adaptive Protection |
| 24/7 expert team | ✅ DRR team (Standard tier) | ✅ DRT team (Advanced) | ✅ DRR team (Plus) |
| Cost protection | ✅ Yes (Standard) | ✅ Yes (Advanced) | ✅ Credits (Plus) |
| Network analysis | ✅ Security Director (new) | ✅ Security Director (new) | ⚠️ Via Security Command Center |
| Transparent inline | ✅ Yes | ✅✅ Zero latency overhead | ✅ Yes |
| Global edge locations | 180+ | 450+ | 100+ |
| Published attack size | ✅ 15.72 Tbps (Oct 2025) | ⚠️ Not recent | ✅ 398M RPS (2023) |
| Multi-cloud support | ⚠️ Limited | ❌ AWS-only | ⚠️ Limited |
Strengths and Weaknesses
Microsoft Azure DDoS Protection
Strengths:
- ✅ Excellent integration across Azure ecosystem
- ✅ Proven capability against record-breaking volumetric attacks (15.72 Tbps)
- ✅ Comprehensive global footprint
- ✅ Mature machine learning-based detection
- ✅ New Network Security Director for proactive defense
- ✅ Transparent operation with minimal customer configuration
Weaknesses:
- ⚠️ Layer 7 protection requires separate WAF configuration
- ⚠️ Less emphasis on ML-automated rule generation compared to Google
- ⚠️ Standard tier pricing can be expensive for smaller workloads
Best for: Organizations heavily invested in Azure ecosystem, those requiring proven large-scale attack defense, enterprises wanting integrated protection across Azure services.
Amazon AWS Shield
Strengths:
- ✅ Largest global edge network (450+ PoPs)
- ✅ True zero-latency inline protection
- ✅ Excellent integration with CloudFront and Route 53
- ✅ Transparent operation requiring no architecture changes
- ✅ Mature service with years of production use
- ✅ DRT team access with proactive engagement option
Weaknesses:
- ⚠️ Shield Advanced pricing ($3K/month minimum) can be expensive
- ⚠️ Less sophisticated ML/AI capabilities compared to Google
- ⚠️ Limited public information about recent attack mitigations
- ⚠️ Layer 7 protection requires AWS WAF configuration and management
Best for: Organizations using CloudFront and Route 53 heavily, those requiring true zero-latency protection, enterprises wanting mature, proven defense with expert support.
Google Cloud Armor
Strengths:
- ✅✅ Best-in-class ML/AI with Adaptive Protection
- ✅ Leverages Google's massive infrastructure and expertise
- ✅ Automated custom rule generation
- ✅ Excellent Layer 7 attack protection
- ✅ Proven against sophisticated application-layer attacks
- ✅ Strong bot management capabilities
Weaknesses:
- ⚠️ Smaller global edge network compared to AWS
- ⚠️ Requires load balancer for protection (not all resources covered)
- ⚠️ Less mature network analysis tools compared to Azure/AWS new offerings
- ⚠️ Google Cloud's smaller market share means less field testing
Best for: Organizations facing sophisticated Layer 7 attacks, those wanting cutting-edge ML/AI capabilities, enterprises with security teams that value automated intelligence over manual control.
Cost Comparison
Azure DDoS Protection Standard
- Cost: Approximately $2,944/month per protected resource
- Includes: 100 resources, additional resources ~$30/month each
- Overage: Data processing charges for traffic over thresholds
AWS Shield Advanced
- Cost: $3,000/month per organization (not per resource)
- Includes: Protection for unlimited resources
- Overage: Data transfer fees apply (but with cost protection during attacks)
Google Cloud Armor Managed Protection Plus
- Cost: $3,000/month per project
- Includes: All resources in the project
- Overage: Request processing fees and rule evaluation fees
Winner: AWS Shield Advanced offers the best value for organizations with many resources, as it covers unlimited resources for a flat monthly fee. Azure and Google charge per resource or project.
Performance Comparison
Latency Impact
All three providers claim minimal latency impact:
- AWS Shield: True inline with claimed "zero additional latency"
- Azure: < 1ms typical latency addition
- Google: < 1ms typical latency addition
In practice, the latency impact is negligible for all three solutions in most scenarios.
Detection Speed
All three providers detect attacks within seconds:
- Azure: "Within seconds" of attack start
- AWS: "Under 1 second" detection
- Google: "Subsecond" detection
Realistically, all three are fast enough that detection speed isn't a meaningful differentiator.
Mitigation Speed
More variation exists in mitigation activation:
- Azure: Mitigation within seconds of detection
- AWS: "Instant" mitigation (already inline)
- Google: Mitigation within seconds (with Adaptive Protection adding 2-5 minutes for custom rules)
Winner: AWS Shield's always-inline architecture provides the fastest mitigation activation, though the difference is minor for most scenarios.
Sophistication of Threats Defended
Volumetric Attacks (Layer 3/4)
All three providers excel at defending against volumetric attacks:
- ✅ Azure: Proven against 15.72 Tbps
- ✅ AWS: Defended against multi-Tbps attacks (specific sizes not published)
- ✅ Google: Infrastructure routinely handles 40-50 Tbps of legitimate traffic
Application Layer Attacks (Layer 7)
Differences emerge for sophisticated application attacks:
- ⚠️ Azure: Good WAF integration but requires manual rule management
- ⚠️ AWS: Good WAF integration but requires manual rule management
- ✅✅ Google: Adaptive Protection automatically generates custom rules
Winner: Google Cloud Armor's Adaptive Protection provides a significant advantage for defending against novel, sophisticated application-layer attacks.
Operational Complexity
Ease of Initial Setup
- Azure: Simple for standard scenarios, complex for advanced configurations
- AWS: Moderately complex (Shield Advanced requires setup)
- Google: Simple setup, complexity in policy fine-tuning
Ongoing Management
- Azure: Low maintenance once configured
- AWS: Low maintenance, DRT available for complex attacks
- Google: Lowest maintenance due to Adaptive Protection automation
Winner: Google Cloud Armor requires the least ongoing operational effort, especially for application-layer attack defense.
The Verdict: Which Provider is Best?
There is no universal "best" DDoS protection—the right choice depends on your specific context:
Choose Azure DDoS Protection if:
- You're heavily invested in the Azure ecosystem
- You need proven defense against the largest volumetric attacks
- You want integrated protection across all Azure services
- You're willing to invest in configuring comprehensive security policies
Choose AWS Shield if:
- You're using CloudFront, Route 53, or other AWS edge services extensively
- You want true zero-latency inline protection
- You need to protect a large number of diverse resources cost-effectively
- You want mature, battle-tested defense with extensive AWS integration
Choose Google Cloud Armor if:
- You face sophisticated application-layer attacks
- You want cutting-edge ML/AI-powered automated defense
- You value automated custom rule generation over manual control
- You're running global applications on Google Cloud infrastructure
The Multi-Cloud Reality
Many enterprises use multiple cloud providers and should implement DDoS protection on each:
- Defense in depth: Provider-specific attacks require provider-specific defenses
- Architectural diversity: Different providers excel against different attack types
- Redundancy: If one provider faces outages, others maintain service
- Specialization: Use each provider's strengths for appropriate workloads
Rather than choosing one "winner," sophisticated organizations implement best-of-breed solutions across their multi-cloud architecture.
The IoT Problem: Why Attacks Keep Getting Bigger
The Root Cause of Massive DDoS Attacks
Every record-breaking DDoS attack in 2025 shares a common source: compromised Internet of Things (IoT) devices. Understanding why IoT devices have become the primary vector for DDoS attacks reveals why attacks keep growing despite increased defensive capabilities.
The Perfect Storm: Why IoT Devices Are Ideal for Botnets
Massive and Growing Install Base
The IoT device population has exploded:
- 14.4 billion connected IoT devices worldwide as of 2024
- 25+ billion projected by 2030
- Devices include: routers, IP cameras, smart TVs, DVRs, printers, smart home devices, industrial sensors
Each device represents a potential bot in a massive attack botnet.
Always-On, Always-Connected
Unlike PCs and phones that sleep or disconnect:
- IoT devices typically run 24/7
- Continuously connected to internet
- Often on high-bandwidth residential or business connections
- Minimal legitimate traffic (easy for attackers to use full bandwidth)
High-Bandwidth Connections
Modern internet connections provide massive bandwidth:
- Gigabit fiber: 1 Gbps upload (1-10 Gbps common in urban areas)
- Cable internet: 20-50 Mbps typical upload
- 5G cellular: 100+ Mbps upload
A botnet of just 10,000 gigabit-connected devices could theoretically generate 10 Tbps of attack traffic.
Weak Security Posture
IoT devices are notoriously insecure:
Default Credentials
- Many devices ship with default usernames/passwords (admin/admin, root/password)
- Users rarely change these defaults
- Manufacturers don't enforce password changes
- Same credentials often used across entire product line
Lack of Updates
- Many devices never receive security updates
- Update mechanisms often insecure or non-existent
- Manufacturers abandon support quickly
- Users don't know how to update devices
Unnecessary Exposure
- Management interfaces exposed directly to internet
- No firewall protection on many devices
- UPnP automatically opens firewall holes
- Devices trust local network traffic
Minimal Security Features
- No host-based firewalls
- No intrusion detection
- No endpoint protection software
- No security monitoring or logging
Limited Owner Visibility
Most owners don't know their devices are compromised:
- No obvious symptoms (device functions normally)
- No antivirus scanning
- No security monitoring
- No way to detect compromise
Devices can participate in attacks for months or years without owner awareness.
The Supply Chain Attack Advantage
Recent botnet evolution has focused on supply chain compromise, dramatically increasing infection efficiency:
Traditional Botnet Building
Historically, botnets grew by:
- Scanning internet for vulnerable devices
- Exploiting security vulnerabilities
- Installing malware
- Adding device to botnet
- Repeat
This process is slow, requiring millions of scan attempts per compromised device.
Modern Supply Chain Compromise
New approach as demonstrated by Aisuru:
- Compromise device manufacturer's update server
- Inject malware into legitimate firmware updates
- Manufacturer distributes weaponized updates
- Devices automatically download and install malware
- Thousands of devices compromised instantly
This approach is vastly more efficient:
- No scanning required
- No exploitation necessary
- Updates cryptographically signed (appear legitimate)
- Devices actively pull malware
- Security-conscious users affected (they update regularly)
Case Study: The Totolink Compromise
The April 2025 compromise of Totolink's update infrastructure demonstrates the supply chain threat:
The Attack
Attackers compromised Totolink's firmware update server through an unpatched vulnerability. Once inside, they:
- Modified legitimate firmware updates by injecting Aisuru botnet code
- Signed modified updates using Totolink's legitimate signing keys
- Replaced legitimate updates on download server with weaponized versions
- Maintained access for weeks to continuously distribute malware
The Impact
- 100,000+ devices infected within days
- Global distribution across all Totolink customer markets
- Undetectable by users (updates appeared legitimate)
- Persistent (malware survived reboots and configuration resets)
The Response
Totolink's response was criticized as inadequate:
- 7 days to publicly acknowledge compromise
- 14 days to release clean firmware
- No automatic remediation (users had to manually reinstall firmware)
- No notification to most affected customers
Many compromised devices remain infected as of November 2025.
The Economic Incentives
IoT insecurity persists because of misaligned economic incentives:
Manufacturer Incentives
Device manufacturers prioritize:
- Cost reduction: Security features increase costs
- Time to market: Security testing delays launches
- Feature differentiation: Marketing focuses on features, not security
- Minimal liability: Few consequences for shipping insecure devices
Manufacturers have little incentive to invest in security because:
- Consumers don't demand it (security invisible until breach)
- No regulations require it (in most markets)
- Competitors shipping insecure devices have cost advantage
- Liability for insecurity is minimal
Consumer Incentives
Consumers prioritize:
- Price: Cheap devices attractive regardless of security
- Features: Visible functionality over invisible security
- Convenience: Security often makes devices harder to use
Consumers can't effectively evaluate security:
- No standardized security ratings
- Technical knowledge required to assess
- Security only matters after breach
- Individual impact of compromise is low
ISP Incentives
Internet Service Providers could help but prioritize:
- Customer satisfaction: Blocking attacks might affect legitimate traffic
- Cost minimization: DDoS filtering infrastructure is expensive
- Simplicity: Identifying compromised devices is complex
- Legal concerns: Monitoring customer devices raises privacy questions
ISPs face little pressure to address DDoS because:
- Victims are usually not their customers
- Attacks originate from many ISPs simultaneously
- Costs of defense exceed costs of doing nothing
- Regulatory requirements are minimal
The Regulatory Response (or Lack Thereof)
Governments have been slow to address IoT security despite years of warnings:
United States
Limited progress:
- IoT Cybersecurity Improvement Act (2020): Minimal requirements only for federal government purchases
- NIST guidelines: Voluntary recommendations, not requirements
- State laws: California and Oregon passed IoT security laws, but requirements are minimal
- No federal mandate: No comprehensive IoT security requirements for consumer devices
European Union
Somewhat more aggressive:
- Cyber Resilience Act (2024): Requires security updates for "essential" IoT devices
- Radio Equipment Directive: Includes some security requirements
- GDPR: Privacy requirements indirectly improve security
- Implementation delayed: Most requirements don't take effect until 2026-2027
Asia
Variable approaches:
- China: Cybersecurity Law requires device security but enforcement is inconsistent
- Japan: Guidelines but no mandatory requirements
- South Korea: Some requirements for critical infrastructure
- Singapore: Cybersecurity labeling scheme (voluntary)
Potential Solutions
Addressing the IoT DDoS problem requires coordinated action across multiple stakeholders:
Manufacturer Accountability
- Mandatory security standards: Minimum requirements for IoT devices
- Security labeling: Standardized ratings so consumers can make informed choices
- Update requirements: Mandate security updates for minimum device lifetime
- Liability frameworks: Make manufacturers liable for damages from insecure devices
- Secure-by-default: Eliminate default credentials, require strong passwords
ISP Responsibilities
- BCP 38 implementation: Prevent IP address spoofing (blocks amplification attacks)
- Outbound traffic filtering: Detect and block DDoS traffic from residential connections
- Customer notification: Alert customers when devices are compromised
- Network segmentation: Isolate IoT devices on separate network segments
- Quarantine capabilities: Temporarily restrict compromised devices
Consumer Education
- Security awareness: Help consumers understand IoT risks
- Simple security tools: Easy-to-use network monitoring and device management
- Update campaigns: Encourage regular firmware updates
- Secure configuration: Guidance on changing defaults and hardening devices
International Cooperation
- Information sharing: Cross-border threat intelligence on botnets
- Coordinated takedowns: Joint law enforcement operations against botnet operators
- Harmonized regulations: Consistent security requirements across markets
- Technical standards: International cooperation on IoT security standards
The Brutal Reality
Despite years of warnings and multiple high-profile attacks, IoT security remains abysmal. Until economic incentives align or regulations mandate change, IoT-based DDoS attacks will continue to grow in scale and frequency.
The cloud providers' defensive capabilities are improving rapidly—but so is the attack infrastructure. It's an arms race with no end in sight.
Beyond DDoS: The Broader Resilience Challenge
DDoS attacks are just one threat vector facing cloud infrastructure. Even with perfect DDoS defense, cloud services face numerous other resilience challenges that can cause outages affecting millions of users.
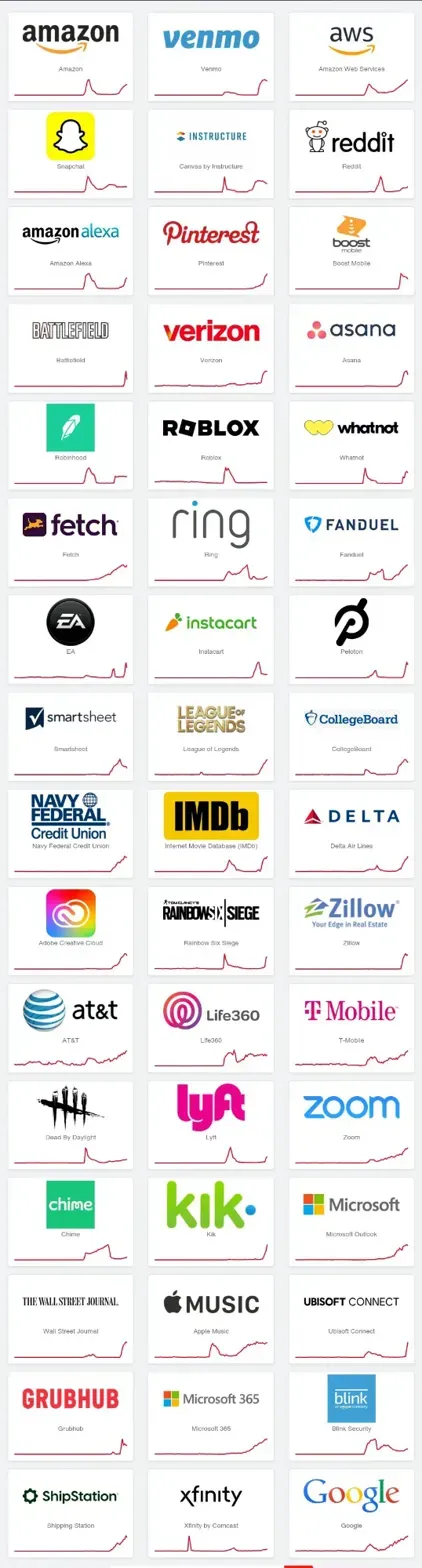
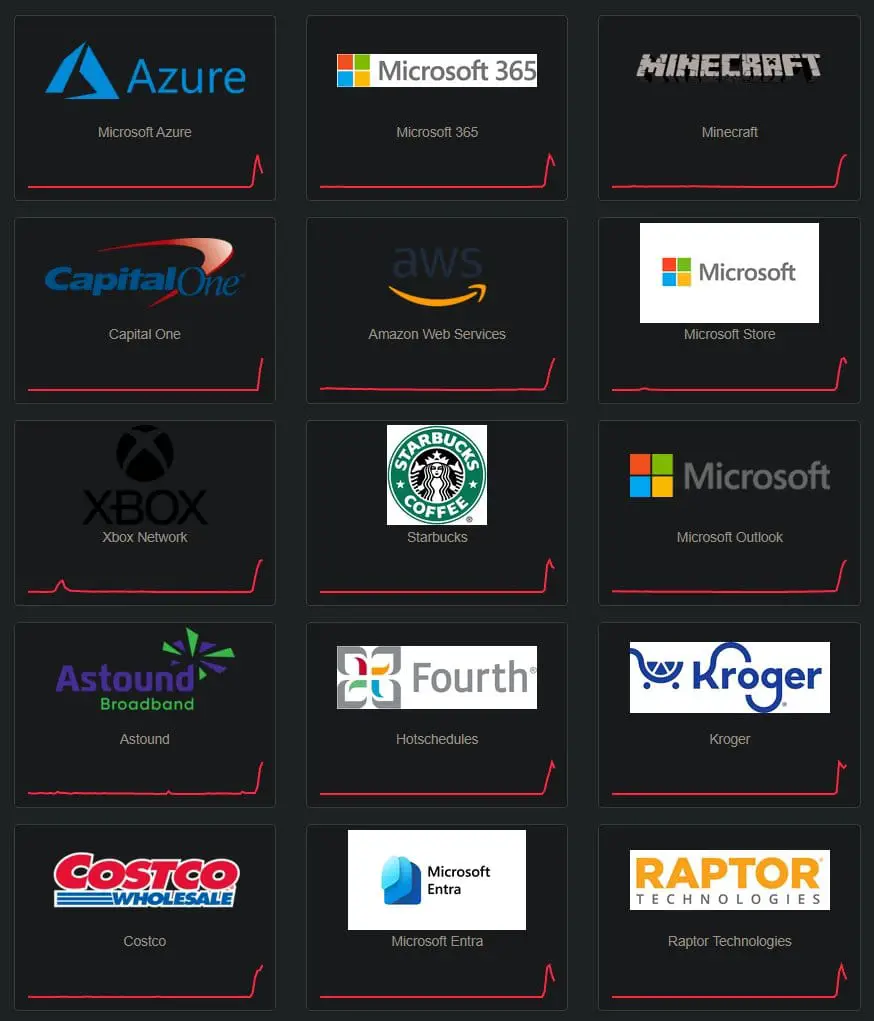
The Azure Front Door Outage: When Configuration Errors Cascade
On August 30, 2025, Microsoft's Azure Front Door service experienced a global outage that lasted over four hours, affecting thousands of websites and applications worldwide. This incident demonstrated that even sophisticated cloud providers face risks beyond external attacks.
What Happened
A configuration change to Azure Front Door's routing logic contained an error that caused:
- Cascading failures as healthy nodes tried to compensate for failing nodes
- Amplification effect where the error's impact multiplied across Azure's global network
- Service degradation even for customers not directly affected by the configuration change
- Extended recovery time as Microsoft struggled to identify and roll back the problematic change
The Lessons
This outage revealed several critical points:
- Complexity breeds fragility: Azure's globally distributed architecture, while providing DDoS resilience, creates complex failure modes
- Configuration is critical: Software bugs can be fixed, but configuration errors can cause immediate, widespread impact
- Defense in depth isn't enough: Azure had monitoring, automated health checks, and redundancy—but a configuration error bypassed these protections
- Recovery is challenging: Identifying which of thousands of recent changes caused an outage takes time, even with sophisticated tooling
When the Cloud Falls: Third-Party Dependencies
The broader challenge of cloud resilience extends beyond individual provider capabilities. As detailed in "When the Cloud Falls: Third-Party Dependencies and the New Definition of Critical Infrastructure", modern cloud architecture creates complex dependency chains where failure of a single service can cascade across the internet.
The Dependency Problem
Organizations building on cloud infrastructure depend on:
- Cloud provider infrastructure: Azure, AWS, Google Cloud platforms themselves
- Cloud provider services: Managed databases, load balancers, CDNs
- Third-party SaaS: Authentication (Auth0), monitoring (Datadog), logging (Splunk)
- Open-source dependencies: Libraries, frameworks, tools
- Internet infrastructure: DNS providers, BGP routing, submarine cables
A failure at any layer can cause outages affecting numerous dependent services.
Recent Examples
- Cloudflare outage (November 2025): Took down portions of X (Twitter), ChatGPT, McDonald's websites, and thousands of other services
- CrowdStrike update (July 2024): Defective security software update crashed millions of Windows systems globally
- AWS us-east-1 outage (2023): Single region failure affected services worldwide due to control plane dependencies
The Disaster Recovery Imperative
For organizations building on cloud infrastructure, the combination of DDoS threats, provider outages, and dependency failures creates an imperative for comprehensive disaster recovery planning:
Multi-Cloud Architecture
Don't put all eggs in one basket:
- Distribute workloads across multiple cloud providers
- Maintain failover capabilities to switch providers during outages
- Test regularly to ensure failover actually works
- Accept complexity of managing multiple cloud platforms
Regional Redundancy
Even within a single cloud:
- Deploy across multiple regions within each cloud provider
- Use active-active architecture rather than hot standby
- Consider geographic distribution for resilience against regional disasters
- Account for data residency requirements when choosing regions
Dependency Management
- Map all dependencies to understand failure modes
- Implement circuit breakers to prevent cascading failures
- Maintain fallback options for critical third-party services
- Monitor third-party health to detect issues early
Testing and Validation
- Regular disaster recovery drills simulating various failure scenarios
- Chaos engineering to identify weaknesses before real incidents
- Load testing to understand system limits
- Table-top exercises to prepare incident response teams
The Shared Responsibility Model
Cloud providers clearly state that security and availability are shared responsibilities:
Provider Responsibilities:
- Infrastructure security and DDoS protection
- Physical data center security
- Network security and availability
- Platform service availability
Customer Responsibilities:
- Application architecture and resilience
- Data backup and disaster recovery planning
- Multi-region and multi-cloud strategy
- Security configuration and monitoring
The Critical Point: Even with perfect cloud provider DDoS defense, customers are responsible for ensuring their applications remain available during outages. This requires intentional architecture, investment in redundancy, and regular testing.
The Business Continuity Perspective
From a business continuity standpoint, organizations must consider:
Risk Assessment
- What is the impact of cloud service outage?
- How long can the business operate without cloud services?
- What is the financial impact of downtime?
- What are regulatory or contractual availability requirements?
Investment Decisions
- Cost of multi-cloud architecture vs. risk of single-cloud outage
- Cost of redundancy vs. cost of downtime
- Internal expertise required for complex resilient architectures
- Opportunity cost of engineering time spent on resilience vs. features
Strategic Planning
- Long-term cloud provider relationships and dependencies
- Build vs. buy decisions for critical infrastructure
- Geographic expansion and regulatory requirements
- Merger, acquisition, and divestiture impacts on cloud architecture
The record-breaking DDoS attacks of 2025 demonstrate that cloud providers can defend against unprecedented threats—but they also highlight that no provider is immune to outages. Organizations must take ownership of their resilience strategy.
What This Means for Your Organization
Immediate Actions for Security Teams
Based on the threats and defenses analyzed in this article, security teams should take these immediate actions:
1. Verify DDoS Protection Configuration
- Audit current protection: Identify which cloud provider DDoS services are enabled
- Check coverage: Ensure all internet-facing resources are protected
- Review configurations: Verify protection matches application traffic patterns
- Enable logging: Ensure attack telemetry is being captured for analysis
Most organizations don't fully leverage the DDoS protection included with their cloud services. Start by ensuring you're getting the protection you're already paying for.
2. Assess Current Resilience
- Document dependencies: Map all cloud services, third-party services, and dependencies
- Identify single points of failure: Where could a single failure cause total outage?
- Review disaster recovery plans: When was the last DR test? Did it work?
- Calculate risk exposure: What's the business impact of various outage scenarios?
You can't protect what you don't understand. Start with visibility into your current architecture and risks.
3. Test Your Defenses
- Conduct DDoS simulation: Work with your cloud provider to test DDoS mitigation
- Run failover drills: Validate that multi-region/multi-cloud failover actually works
- Load test applications: Understand your performance limits before attackers find them
- Practice incident response: Table-top exercises prepare teams for real incidents
Untested disaster recovery plans are fiction. Only actual testing reveals whether your defenses work.
Strategic Recommendations for Leadership
1. Treat Cloud Resilience as a Business Priority
Cloud availability isn't just a technical concern—it's a business risk requiring executive attention:
- Board-level reporting: Cloud resilience should be part of regular risk reporting
- Investment prioritization: Allocate sufficient budget for redundancy and resilience
- Organizational ownership: Clearly assign responsibility for cloud resilience strategy
- Incentive alignment: Include availability metrics in team and leadership objectives
2. Embrace Multi-Cloud Strategy (Carefully)
Multi-cloud provides resilience but adds complexity:
- Start with critical workloads: Don't try to multi-cloud everything at once
- Focus on portability: Design applications to be cloud-agnostic
- Accept higher costs: Redundancy and abstraction layers cost money
- Build expertise: Invest in training teams on multiple cloud platforms
Multi-cloud is not a silver bullet—it trades single-provider risk for operational complexity.
3. Invest in Proactive Defense
Reactive incident response is insufficient for modern threats:
- Threat intelligence: Subscribe to cloud provider security advisories and threat feeds
- Continuous monitoring: Real-time visibility into application and infrastructure health
- Automated response: Implement automated remediation for common failure scenarios
- Regular reviews: Quarterly architecture reviews to identify emerging risks
The gap between threat sophistication and defensive capabilities is narrowing. Proactive investment is essential.
Specific Guidance by Cloud Provider
If You're on Azure:
- ✅ Enable DDoS Protection Standard for critical workloads (cost: ~$3K/month)
- ✅ Configure Azure Front Door with WAF for application-layer protection
- ✅ Deploy across multiple regions using Traffic Manager for failover
- ✅ Use Azure Security Center to monitor for configuration issues
- ✅ Engage with DDoS Rapid Response team during significant attacks
- ✅ Leverage new Network Security Director (in preview) for proactive analysis
If You're on AWS:
- ✅ Enable Shield Advanced if you're spending significantly on AWS ($3K/month flat fee protects everything)
- ✅ Use CloudFront and Route 53 for edge protection and global distribution
- ✅ Configure AWS WAF with AWS Managed Rules for baseline application protection
- ✅ Grant DRT proactive engagement permission for automated response during attacks
- ✅ Implement multi-region architecture using Route 53 health checks and failover routing
- ✅ Use Shield's Network Security Director (preview) to identify configuration gaps
If You're on Google Cloud:
- ✅ Enable Cloud Armor Managed Protection Plus for premium ML-powered defense
- ✅ Configure Adaptive Protection to automatically generate custom security rules
- ✅ Use global load balancers to leverage Google's massive global network
- ✅ Enable pre-configured WAF rules for OWASP Top 10 protection
- ✅ Deploy across multiple regions for resilience
- ✅ Leverage Security Command Center for unified security monitoring
The Bottom Line
The good news: Major cloud providers have invested billions in DDoS defense. Their systems can stop attacks that would have been unimaginable just years ago. If you're running on Azure, AWS, or Google Cloud, you have access to world-class protection.
The bad news: Attacks are growing faster than defenses. The same IoT infrastructure that enables massive attacks continues to expand. Supply chain compromises are giving botnet operators unprecedented infection capabilities. And DDoS is just one of many threats to cloud availability.
The reality: Organizations must take ownership of their resilience strategy. Cloud provider DDoS protection is necessary but not sufficient. You need:
- Proper configuration and monitoring
- Multi-region and multi-cloud redundancy
- Regular testing and validation
- Incident response preparation
- Business continuity planning
The digital tsunamis will keep coming. The question is whether your organization will be ready when they hit.
Conclusion: The Infinite Arms Race
On October 24, 2025, Microsoft Azure automatically detected and neutralized a 15.72 Tbps DDoS attack in seconds. Not a single customer experienced downtime. This represents an extraordinary technological achievement—a testament to billions of dollars of investment, sophisticated machine learning, and global infrastructure operating at unprecedented scale.
Yet just weeks earlier, Cloudflare faced an even larger 22.2 Tbps attack. And within months, these records will almost certainly be broken again.
We are witnessing an infinite arms race between attackers and defenders.
On one side: Cloud providers investing billions in defense, leveraging AI and machine learning, operating globally distributed infrastructure, and continuously evolving their capabilities.
On the other side: Botnet operators exploiting hundreds of thousands of insecure IoT devices, compromising supply chains, launching attacks of exponentially growing scale, and continuously innovating new techniques.
Neither side is winning. Both are locked in perpetual escalation.
For organizations building on cloud infrastructure, several truths are now clear:
- The cloud providers are doing their part. Azure, AWS, and Google have built impressive DDoS defenses that successfully protect against unprecedented threats.
- But no provider is invulnerable. Configuration errors, software bugs, and cascading failures can cause outages even when external attacks are successfully defended.
- Responsibility is shared. Cloud providers protect their infrastructure. Customers must architect applications for resilience and maintain disaster recovery capabilities.
- Complexity is unavoidable. Multi-cloud, multi-region architectures add operational complexity but provide essential redundancy.
- Testing is mandatory. Untested disaster recovery plans will fail when needed. Regular testing is the only way to validate resilience.
- IoT is the perpetual problem. Until economic incentives change or regulations mandate security, IoT devices will continue fueling massive attacks.
- The stakes keep rising. As more critical infrastructure moves to the cloud, the impact of successful attacks or provider outages affects an ever-larger portion of the economy and society.
The question facing every CISO, CTO, and business leader in 2025 is not whether your cloud provider can defend against DDoS attacks—Microsoft, Amazon, and Google have proven they can stop even record-breaking attacks.
The question is whether your organization has architected your applications and operations to remain resilient when the inevitable happens: when a DDoS attack does break through, when a cloud provider has an outage, when a third-party service fails, when a configuration error cascades into a major incident.
The digital tsunamis will keep coming. Some will be stopped. Others will break through. The organizations that survive and thrive will be those that planned for both scenarios.
The arms race continues. Choose your defenses wisely.
References and Further Reading
- Microsoft Azure Blog: "Defending the cloud: Azure neutralized a record-breaking 15 Tbps DDoS attack" (November 2025)
- Cloudflare Blog: "Cloudflare mitigates new record-breaking 22.2 Tbps DDoS attack" (September 2025)
- Cloudflare: "Record-breaking 5.6 Tbps DDoS attack and global DDoS trends for 2024 Q4"
- Google Cloud Blog: "Google Cloud mitigated largest DDoS attack, peaking above 398 million rps" (2023)
- Bleeping Computer: "Microsoft: Aisuru botnet used 500,000 IPs in 15 Tbps Azure DDoS attack" (November 2025)
- The Register: "'Largest-ever' cloud DDoS attack pummels Azure with 3.64B packets per second" (November 2025)
- Tom's Hardware: "Microsoft Azure Blocks Largest DDoS Attack in History" (November 2025)
- Breached: "Microsoft's Azure Front Door Outage: How a Configuration Error Cascaded into Global Service Disruption"
- Breached: "When the Cloud Falls: Third-Party Dependencies and the New Definition of Critical Infrastructure"