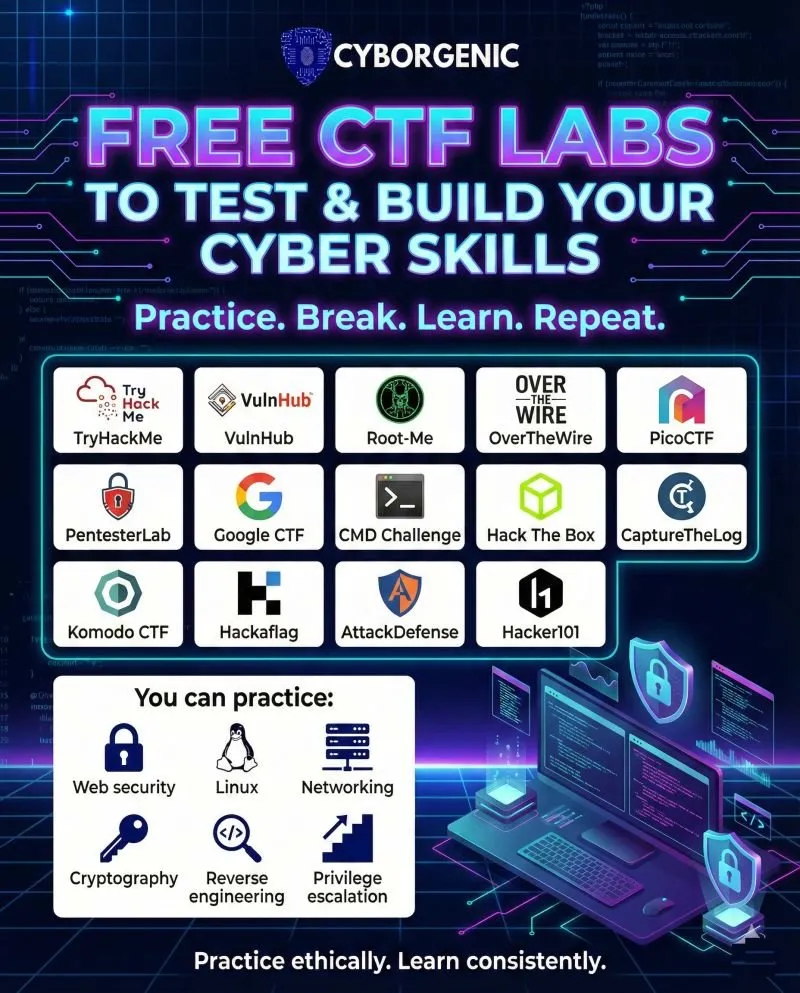
The Hacker's Dojo: A Complete Technical Brief on Free CTF Labs & Practice Platforms (2026)

Why Practice Matters More Than Theory
You can watch a thousand YouTube tutorials on SQL injection and still freeze the first time a real login form stares back at you. CTFs — Capture the Flag competitions — fix that. They drop you into real attack-and-defend scenarios where the only way forward is to break something. And the best part? Most of the top platforms are completely free.
This guide covers every platform in the Cyborgenic infographic that's been floating around the community, plus several heavy-hitters the graphic missed. Think of this as your technical brief: what each platform actually does, who it's for, what skill categories it trains, and how to stack them for maximum learning velocity.

The Platforms: A Technical Breakdown
1. TryHackMe
URL: tryhackme.com | Skill Level: Beginner–Intermediate | Free Tier: Yes
TryHackMe is the most beginner-friendly entry point in the space. It wraps CTF-style challenges inside structured "rooms" — self-contained learning modules with guided instructions, embedded hints, and browser-based attack machines that require zero local setup. You attack everything through a browser or OpenVPN connection directly from your laptop.
What you'll practice: Web security, Linux fundamentals, network enumeration, OSINT, privilege escalation, Active Directory basics, and more. The Pre-Security and Introduction to Cyber Security learning paths are genuinely excellent for absolute beginners.
Technical edge: The "AttackBox" feature lets you spin up a Kali Linux instance in your browser — no VM required. This is particularly useful if you're learning from a locked-down work laptop or Chromebook.
Pro tip: Complete the "Jr Penetration Tester" path before jumping to Hack The Box. It will save you hours of confusion.
2. VulnHub
URL: vulnhub.com | Skill Level: Intermediate–Advanced | Free Tier: Entirely Free
VulnHub is the offline hacker's paradise. Instead of a browser-based platform, it hosts hundreds of downloadable vulnerable virtual machine images (.ova and .vmdk formats) that you import into VirtualBox or VMware Workstation on your local machine.
What you'll practice: The full penetration testing lifecycle — reconnaissance, enumeration, exploitation, post-exploitation, and privilege escalation. Because these are full OS images, you encounter realistic system configurations rather than isolated challenge boxes.
Technical edge: You control the entire lab. Snapshots, network isolation, packet captures with Wireshark running in parallel — all of it. This makes VulnHub ideal for building your home lab methodology before OSCP.
Best starter VMs: Kioptrix (series 1–5), Mr. Robot, SkyDog, and the DC series. Start with Kioptrix 1 to get your bearings.
3. Root-Me
URL: root-me.org | Skill Level: Beginner–Advanced | Free Tier: Yes (most challenges)
Root-Me is the European dark horse of CTF platforms with over 500 challenges spanning a wider technical breadth than most competitors. It's less gamified than TryHackMe, more challenge-focused, and the community skews toward French-speaking practitioners — though the platform is fully bilingual.
What you'll practice: Web server/client exploitation, network forensics, programming puzzles, cracking, steganography, reverse engineering, and app/system exploitation. The diversity here is exceptional.
Technical edge: Root-Me hosts persistent virtual environments where you can interact with actual running services — SSH into real machines, connect to live web servers — rather than just answering trivia questions about vulnerabilities.
Worth noting: The scoring system and challenge categories make it excellent for identifying specific skill gaps. If you're weak on network forensics or steganography, Root-Me has more quality content in those areas than almost any other platform.
4. OverTheWire
URL: overthewire.org | Skill Level: Beginner–Advanced | Free Tier: Entirely Free
OverTheWire runs "wargames" — progressive challenge series accessed entirely via SSH. There are no flashy dashboards. You connect to a remote server, solve a puzzle to find a password, and use that password to reach the next level. It's deliberately stripped down.
What you'll practice: The Bandit wargame (levels 0–34) is the definitive beginner introduction to Linux command-line hacking — file permissions, SSH, bash scripting, process manipulation, and cryptography primitives. After Bandit, graduate to Natas (web), Leviathan (setuid binaries), Krypton (cryptography), and Narnia (binary exploitation).
Technical edge: OverTheWire teaches you to be comfortable in an SSH shell with nothing but man pages and your own problem-solving. That discomfort is the point. Professionals who can operate efficiently in a bare terminal are significantly more effective in real engagements.
Starting command:
ssh bandit0@bandit.labs.overthewire.org -p 2220
# Password: bandit0
5. PicoCTF
URL: picoctf.org | Skill Level: Beginner–Intermediate | Free Tier: Entirely Free
PicoCTF is produced by Carnegie Mellon University and is officially aimed at middle and high school students — but don't let that fool you. The challenge archive (picoGym) contains hundreds of well-designed problems that adult learners use to fill fundamental gaps in cryptography, binary exploitation, web exploitation, forensics, and reverse engineering.
What you'll practice: All major CTF categories. Crucially, PicoCTF is one of the few platforms with excellent cryptography and binary/forensics content at an accessible difficulty level. Most other beginner platforms gloss over these areas.
Technical edge: The annual PicoCTF competition (typically March) draws 50,000+ participants globally, making it an excellent first competition experience. The picoGym archive lets you practice year-round.
Best use case: If you're hitting a wall on crypto or forensics challenges elsewhere, spend a week in picoGym. The explanations and community writeups are some of the best available.
6. PentesterLab
URL: pentesterlab.com | Skill Level: Beginner–Advanced | Free Tier: Yes (Pro plan required for most content)
PentesterLab takes a different approach: rather than just giving you a box to exploit, it teaches you the underlying vulnerability concept through curated exercises and then hands you a lab to practice it immediately. The methodology is tightly aligned with OWASP Top 10 and web application penetration testing.
What you'll practice: SQL injection (manual and blind), XSS (stored, reflected, DOM), CSRF, XXE, SSRF, command injection, file inclusion, deserialization, and authentication bypass. The Pro subscription unlocks badges that are recognized by some employers.
Technical edge: PentesterLab's exercises are grounded in real CVEs and historical vulnerabilities. You're not exploiting made-up problems — you're learning patterns that appear in real bug bounty programs and client engagements.
7. Google CTF
URL: capturetheflag.withgoogle.com | Skill Level: Advanced | Free Tier: Entirely Free
Google CTF is an annual competition run by Google's security team and sits at the higher end of the difficulty spectrum. It is not a beginner platform. Challenges are designed by professional red teamers and often involve cutting-edge exploitation techniques.
What you'll practice: Web exploitation, binary exploitation (pwn), cryptography, reverse engineering, sandbox escapes, and occasionally novel attack categories specific to that year's competition.
Technical edge: The CTF archive hosts all previous years' challenges. Google CTF challenges consistently represent the state of the art in each category and are excellent study material for practitioners preparing for OSCP, OSED, or similar advanced certifications.
Recommended approach: Even if you can't solve most challenges solo, read writeups after the competition ends. The learning density per hour is extremely high.
8. CMD Challenge
URL: cmdchallenge.com | Skill Level: Beginner–Intermediate | Free Tier: Entirely Free
CMD Challenge is narrowly scoped but excellent at what it does: making you faster and more precise with bash. Challenges present specific output requirements and you must write a one-liner that produces the correct result. Each solution runs in a real bash environment.
What you'll practice: Shell scripting, text processing (grep, awk, sed, cut), pipeline construction, file manipulation, and command composition. This directly translates to faster enumeration and post-exploitation work.
Best use case: Pair this with OverTheWire Bandit. They reinforce each other. An hour a week on CMD Challenge will noticeably improve your terminal efficiency within a month.
9. Hack The Box
URL: hackthebox.com | Skill Level: Intermediate–Advanced | Free Tier: Yes (retired machines for free with VIP; some active machines free)
Hack The Box (HTB) is the industry standard for intermediate-to-advanced penetration testing practice. Machines range from easy to insane difficulty and simulate real-world environments including Active Directory forests, multi-pivot scenarios, and realistic misconfigurations.
What you'll practice: Full penetration testing methodology — external reconnaissance, foothold, lateral movement, privilege escalation (Linux and Windows), Active Directory attacks, and pivoting.
Technical edge: HTB's Pro Labs (Offshore, RastaLabs, Cybernetics, APTLabs) simulate entire corporate networks with realistic attack chains. The "Starting Point" section is an excellent bridge between TryHackMe and full HTB machines.
Community resource: 0xdf.gitlab.io hosts detailed writeups for retired HTB machines and is one of the highest-quality technical resources in the community.
OSCP note: Completing 20–30 HTB easy/medium machines is widely considered better OSCP preparation than any paid course alone.
10. CaptureTheLog
URL: capturethelog.com | Skill Level: Beginner–Intermediate | Free Tier: Yes
CaptureTheLog focuses specifically on the blue team — log analysis, SIEM investigations, and threat hunting. This is one of the few CTF-style platforms that doesn't ask you to exploit things, but instead asks you to find evidence that exploitation occurred.
What you'll practice: Log analysis across Windows Event Logs, Linux syslogs, Apache/Nginx access logs, and security tool outputs (Suricata, Zeek). Identifying indicators of compromise, reconstructing attacker timelines, and writing detection logic.
Why it matters: Most CTF practitioners are exclusively offensive. CaptureTheLog rounds out your understanding of what defenders can see — which makes you a better attacker and opens career paths in SOC analysis, threat hunting, and DFIR.
11. Komodo CTF
URL: komodoplatform.com/ctf | Skill Level: Intermediate | Free Tier: Yes
Komodo CTF hosts focused competitions and challenge sets with an emphasis on blockchain and cryptographic challenges, reflecting the platform's roots in the cryptocurrency space. Less well-known than the major platforms, but valuable for practitioners targeting fintech or Web3 security.
What you'll practice: Cryptography, smart contract analysis, and network-layer challenges.
12. Hackaflag
URL: hackaflag.com.br | Skill Level: Beginner–Intermediate | Free Tier: Yes
Hackaflag is a Brazilian-born CTF platform with a strong Latin American community. Challenges span standard CTF categories and the platform hosts regular competitions.
What you'll practice: Web exploitation, forensics, cryptography, and reverse engineering with a community that often produces excellent Portuguese-language writeups and resources.
13. AttackDefense
URL: attackdefense.com | Skill Level: Intermediate–Advanced | Free Tier: Yes (limited; paid tiers expand access significantly)
AttackDefense, operated by Pentester Academy, provides browser-based lab environments for both offensive and defensive skill development. Labs spin up in seconds and cover an enormous range of attack scenarios.
What you'll practice: Network penetration testing, web application attacks, exploit development, Active Directory attacks, vulnerability assessment, and defensive labs for network traffic analysis and incident response.
Technical edge: The lab environments persist for your session and include pre-configured tool sets. It's one of the most comprehensive browser-based practice environments available and is increasingly used by organizations for team training.
14. Hacker101
URL: hacker101.com | Skill Level: Beginner–Intermediate | Free Tier: Entirely Free
Hacker101 is HackerOne's free education platform, purpose-built to funnel practitioners from zero knowledge into active bug bounty hunting. The CTF challenges mirror real-world bug bounty vulnerability classes.
What you'll practice: Web application vulnerabilities — XSS, SQLi, authentication flaws, business logic errors, and API security. Completing Hacker101 CTF challenges earns private invitation points for HackerOne's private bug bounty programs.
Why this matters: Unlike academic CTF platforms, Hacker101 explicitly prepares you to earn money through vulnerability disclosure. The bridge from free practice to paid bug bounty is shorter here than anywhere else in the ecosystem.

The Platforms the Infographic Missed
These didn't make the Cyborgenic graphic but belong in every serious practitioner's rotation:
PortSwigger Web Security Academy (portswigger.net/web-security) — Entirely free, built by the team behind Burp Suite. 200+ interactive labs covering every OWASP category and several cutting-edge attack classes (HTTP request smuggling, web cache poisoning, OAuth vulnerabilities). If web application security is your focus, this is mandatory. The labs are some of the most technically rigorous freely available anywhere, including content based on Black Hat USA 2025 research.
pwn.college (pwn.college) — Arizona State University's free platform for learning binary exploitation from the ground up. Exceptionally well-structured curriculum covering assembly, memory corruption, shellcoding, format strings, and kernel exploitation. If you want to go deep on exploitation development, start here.
LetsDefend (letsdefend.io) — Blue team SOC simulation. Practice triaging alerts, analyzing malware, investigating phishing campaigns, and responding to incidents using realistic SIEM interfaces. Pairs well with CaptureTheLog.
CTFlearn (ctflearn.com) — Community-driven platform with 400+ user-submitted challenges across all major categories. Good for quick daily practice and exposure to the creative challenge design that defines CTF culture.
OffSec Proving Grounds (offensive-security.com/labs) — Three free hours per day of OSCP-style machine access. The paid tier is worth it if you're actively pursuing OSCP; the free tier is useful for sampling the difficulty level.
DVWA (Damn Vulnerable Web Application) — Download and self-host a deliberately insecure PHP/MySQL web app. Covers OWASP Top 10 in an environment you control completely. Ideal for learning to use Burp Suite without time pressure.
Skill Category Mapping
The Cyborgenic infographic highlights six skill areas: web security, Linux, networking, cryptography, reverse engineering, and privilege escalation. Here's how to stack platforms for each:
Web Security: PortSwigger Web Security Academy → Hacker101 → PentesterLab → HackTheBox web challenges
Linux: OverTheWire Bandit → CMD Challenge → TryHackMe Linux paths → VulnHub (CTF VMs)
Networking: TryHackMe (Pre-Security networking module) → OverTheWire Natas → Hack The Box (network-focused machines) → AttackDefense
Cryptography: OverTheWire Krypton → PicoCTF (crypto category) → Root-Me (cryptanalysis section) → Google CTF archive
Reverse Engineering: PicoCTF (RE category) → pwn.college → Root-Me (cracking section) → Hack The Box (RE challenges)
Privilege Escalation: TryHackMe (Linux PrivEsc, Windows PrivEsc rooms) → Hack The Box → VulnHub → OffSec Proving Grounds
Building a 90-Day Practice Stack
Month 1 — Foundation Daily: OverTheWire Bandit (levels 0–20) + CMD Challenge (5 challenges) Weekend: TryHackMe Pre-Security and Linux Fundamentals paths
Month 2 — Web & Enumeration Daily: PortSwigger Web Security Academy (1 lab per day, server-side topics) Weekend: TryHackMe (Jr Penetration Tester path) + Hacker101 CTF (beginner challenges)
Month 3 — Real Machines Daily: PicoCTF archive (fill gaps in crypto/forensics) Weekend: Hack The Box Starting Point → first easy retired machines on VulnHub
After 90 days, you'll have the vocabulary, tooling familiarity, and problem-solving patterns to meaningfully engage with intermediate HTB machines and begin hunting on Hacker101's private programs.
A Note on Mindset
The community has a phrase: "Try Harder." It originated with Offensive Security but applies across every platform here. The instinct to Google the answer the moment you're stuck is the enemy of real skill development. Every hour you spend in the discomfort of not-knowing-yet is compounding.
Use writeups. Read them after you solve something (or after you've genuinely exhausted your attempts), not before. The meta-skill you're really developing across all these platforms isn't any specific technique — it's the ability to sit with an unknown system, form hypotheses, test them systematically, and iterate. That's what penetration testing actually is.
Practice ethically. Learn consistently.
Related Reading on HackerNoob.Tips:
- Top Cybersecurity Platforms for Beginners: A Noob's Guide
- Building Your Own Hacking Lab: A Step-by-Step Guide
- Starting with the Basics: Essential Skills for Aspiring Hackers
- Navigating DEF CON 33: A Survival Guide for First-Timers
- The Psychology of AI Manipulation: How Chatbots Fall for Human Tricks
- Hacking Competitions & Bug Bounty: The Opportunity Map