The Hidden Path to Total Cloud Compromise: Why Your Microsoft Entra ID Roles Need a Security Rethink
A single compromised account can hand attackers the keys to your entire cloud kingdom. Here's how a risk-based privilege framework protects what matters most.
The Wake-Up Call: When Every Tenant Was at Risk
In July 2025, security researcher Dirk-jan Mollema discovered what he called "the most impactful vulnerability" he would probably ever find. CVE-2025-55241 exposed a critical flaw in Microsoft Entra ID that could have allowed any attacker to assume Global Administrator privileges across any tenant in Microsoft's global cloud infrastructure—with a perfect CVSS score of 10.0.

The vulnerability exploited undocumented "Actor tokens" used for internal Microsoft service-to-service communication, combined with a validation failure in the legacy Azure AD Graph API. An attacker needed only a target tenant's public ID and an internal user identifier to impersonate Global Administrators, gaining unrestricted access to modify tenant settings, create identities, and grant any permission.
The most alarming aspect? The attack left virtually no traces. No logs in the victim's tenant. No audit trail. Silent, invisible, and devastating.
While Microsoft patched the vulnerability within three days of disclosure and found no evidence of exploitation in the wild, the incident crystallizes a fundamental truth: identity is the new perimeter, and a single misconfigured privileged account can trigger total tenant compromise.
The Real Problem: Not All Privileged Accounts Are Created Equal
Organizations typically treat privileged access as binary—either you're an admin or you're not. This one-size-fits-all approach creates significant blind spots. A Global Reader receives the same security scrutiny as a Global Administrator, despite vastly different risk profiles. An Application Administrator seems innocuous until you discover it provides a hidden escalation path to Global Admin.
This flat security model is inefficient, creates a false sense of security, and leaves organizations vulnerable to sophisticated attack paths that exploit the interconnected nature of Microsoft Entra ID and Azure RBAC systems.
Consider the Application Administrator role. The name suggests it manages enterprise applications—adding, configuring, or removing them. But the hidden risk? This role can add new credentials to any existing application or service principal in the tenant, including those with Admin Consent for high-privilege API permissions or direct assignment to highly privileged directory roles.
By authenticating as a compromised application using the new credential, an attacker inherits the application's permissions—potentially escalating to Global Administrator and achieving complete tenant compromise with long-term persistence. Once at Global Administrator, they can elevate access to manage all Azure resources by granting themselves the User Access Administrator role at the Azure Root Management Group scope.
This is privilege sprawl in action: seemingly scoped roles that provide indirect paths to total environmental control.
The Attack Surface You Didn't Know You Had
The convergence of identity management (Entra ID), Microsoft 365 services, and infrastructure management (Azure) creates a multi-layered attack surface that most organizations don't fully understand.
Unlike on-premises environments, the cloud control plane is directly accessible from the internet—a globally accessible target. The distinction between roles that manage identity and roles that manage infrastructure continues to blur, magnified by machine identities like service principals that can be impersonated by other identities, creating a complex web of permissions that obscures the true scope of access.
Current Threat Landscape
Recent incidents demonstrate how attackers are actively exploiting these interconnected systems:
Active Account Takeover Campaigns: In early 2025, the UNK_SneakyStrike campaign leveraged the TeamFiltration pentesting framework to target over 80,000 Microsoft Entra ID accounts across approximately 100 cloud tenants. Attackers created Microsoft 365 accounts with valid licenses, leveraged Microsoft Teams API and AWS servers to verify account existence, and performed coordinated password spraying attacks from multiple geographic locations.
RBAC Privilege Escalation Vectors: Researchers have documented multiple Azure RBAC privilege escalation paths, including:
- Azure VM permissions that allow attackers to add SSH public keys and log into VMs running with highly privileged managed identities
- Key Vault Contributor roles that can modify access policies to grant themselves access to secrets, certificates, and keys
- Guest accounts with billing roles creating and transferring Azure subscriptions into target tenants, bypassing typical security controls
Cross-Tenant Attack Paths: The CVE-2025-55241 vulnerability demonstrated how attackers could "hop" across tenants with B2B guest trust relationships, potentially enabling exponential compromise across interconnected cloud ecosystems.
These aren't theoretical risks—they're active attack patterns that sophisticated threat actors are deploying right now.
The Solution: Risk-Based Privilege Framework
A groundbreaking whitepaper from Google Cloud Community security researchers (Razvan Buliga and Ischa Rijff) presents a unified, risk-based privilege framework specifically designed for large organizations managing complex Microsoft Entra ID and Azure environments.
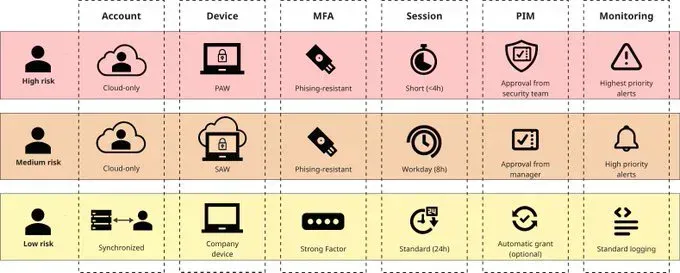
The framework moves beyond Microsoft's standard "privileged" classification for Entra ID roles by introducing a three-tier model that considers scope, attack paths, and potential impact:
High-Risk Roles: The Keys to the Kingdom
Definition: Roles granting ultimate control over identity and/or infrastructure, or providing direct paths to roles that do. Compromise leads to full tenant takeover.
Scope: Tenant-wide, root management groups, or entire environment.
Security Controls:
- Human Identities: Cloud-only accounts on dedicated Physical Privileged Access Workstations (PAW), phishing-resistant MFA (FIDO2, Windows Hello for Business), just-in-time access with security team approval, sessions limited to 4 hours, highest-priority monitoring and alerting
- Machine Identities: Federated or Managed Identities only, short-lived token-based authentication, strict network restrictions, highest-priority anomaly detection
Examples:
- Entra ID: Global Administrator, Privileged Role Administrator, Conditional Access Administrator, Security Administrator, Domain Name Administrator, Hybrid Identity Administrator, Intune Administrator, Privileged Authentication Admin
- Azure: Owner or User Access Administrator at Root Management Group scope
Medium-Risk Roles: High-Value Lateral Targets
Definition: Broad administrative access to specific M365 services, Azure subscriptions, or resource groups. While lacking known direct paths to full compromise, these roles can be leveraged for significant disruption or data loss, and environmental configuration may enable indirect escalation paths.
Scope: Specific M365 services, critical Azure subscriptions, or production management groups.
Security Controls:
- Human Identities: Cloud-only accounts on dedicated Secure Admin Workstations (SAW, can be virtual), phishing-resistant MFA, just-in-time access with manager approval, sessions limited to 8 hours, high-priority alerting
- Machine Identities: Federated or Managed Identities recommended (service principals with certificates acceptable), short-lived tokens or certificates, network restrictions, elevated monitoring
Examples:
- Entra ID: Application Administrator, Cloud Application Administrator, Exchange Administrator, SharePoint Administrator, User Administrator, Authentication Administrator, Global Reader, Directory Writers, Groups Administrator, Windows 365 Administrator
- Azure: Owner or Contributor scoped to business-critical subscriptions or resource groups
Critical Note: The Application Administrator and Cloud Application Administrator roles are classified as medium-risk due to their potential to add credentials to highly privileged service principals, creating indirect Global Admin escalation paths.
Low-Risk Roles: Limited Scope and Impact
Definition: Limited, read-only, or narrowly scoped permissions with minimal systemic security risk.
Scope: Single resources, read-only access, or non-critical operational functions.
Security Controls:
- Human Identities: Regular accounts on standard corporate devices, strong MFA (number matching in Microsoft Authenticator), standard session policies, automatic grant provisioning allowed, standard logging
- Machine Identities: Federated or Managed Identities highly recommended, short-lived tokens or certificates, preferably network-restricted, standard logging with anomaly alerts
Examples:
- Entra ID: Directory Readers, Reports Reader, Application Developer, Message Center Reader, Security Reader
- Azure: Reader at any scope, Contributor scoped to isolated or non-critical resources
Why Azure RBAC Requires Scope-Based Assessment
Unlike Entra ID roles, Azure RBAC privileges are inseparable from scope. An Owner of a single non-critical VM poses far less risk than an Owner at the Root Management Group level.
Risk Classification Matrix:
| Azure Role | Tenant Root / Equivalent MG | Business-Critical Assets | Non-Critical Assets | Limited Scope |
|---|---|---|---|---|
| Owner | High Risk | Medium Risk | Low Risk | Low Risk |
| Contributor | High Risk | Medium Risk | Low Risk | Low Risk |
| User Access Administrator | High Risk | Medium Risk | Low Risk | Low Risk |
| RBAC Administrator | High Risk | Medium Risk | Low Risk | Low Risk |
| Reader | Low Risk | Low Risk | Low Risk | Low Risk |
Any role with write or assignment permissions at the Root Management Group is automatically high-risk because it controls the entire Azure resource hierarchy. An identity with Contributor at this scope could destroy all resources; one with User Access Administrator could grant themselves unlimited access.
Implementation Strategy: Protecting What Matters Most
Organizations should implement this framework using a phased, risk-prioritized approach:
Phase 1: Immediate Actions (Week 1-2)
- Inventory and Classify: Catalog all privileged role assignments across Entra ID and Azure. Use Azure Resource Manager REST API or tools like AzureHound to enumerate roles and permissions.
- Identify High-Risk Exposure: Focus on High-Risk roles first. Document all human and machine identities assigned these roles, their current authentication methods, access devices, and provisioning models.
- Emergency Hardening: For any High-Risk role assignments that don't meet security requirements:
- Implement phishing-resistant MFA immediately
- Enable just-in-time access via Privileged Identity Management
- Restrict to dedicated administrative workstations where possible
- Activate highest-priority monitoring and alerting
Phase 2: Systematic Remediation (Month 1-3)
- High-Risk Role Hardening:
- Deploy dedicated Physical Privileged Access Workstations for Global Administrators and other tenant-wide control roles
- Migrate to cloud-only admin accounts
- Implement 4-hour session limits with required re-authentication
- Configure security-team-approval workflows for role activation
- Deploy comprehensive monitoring for all high-risk role usage
- Medium-Risk Role Protection:
- Deploy Secure Admin Workstations (virtual acceptable via Azure Virtual Desktop)
- Migrate to cloud-only admin accounts for Entra ID roles
- Implement 8-hour session limits
- Configure manager-approval workflows for role activation
- Enable high-priority alerting for anomalous behavior
- Machine Identity Security:
- Migrate service principals to Managed Identities or Federated Identity credentials wherever possible
- Eliminate long-lived client secrets for High-Risk and Medium-Risk roles
- Implement network restrictions (IP allowlists, Azure Private Endpoints)
- Rotate remaining secrets with automated rotation and short expiration periods
Phase 3: Continuous Improvement (Ongoing)
- Attack Path Analysis: Use tools like BloodHound for Entra ID/Azure to identify hidden privilege escalation paths. Pay special attention to:
- Applications and service principals with high-privilege permissions
- Non-role-assignable groups with elevated Azure role assignments or Conditional Access exemptions
- Cross-tenant B2B relationships that could enable tenant-hopping attacks
- Least Privilege Enforcement: Replace broad Owner and Contributor assignments with custom roles that grant only required permissions. Eliminate standing privileges where possible—implement just-in-time elevation for all administrative tasks.
- Hunt for Hidden Risks: Regularly audit for:
- Applications with high-privilege API permissions (RoleManagement.ReadWrite.Directory, User.ReadWrite.All)
- Service principals with Entra ID role assignments
- Guest accounts with Azure subscription access
- Groups that grant elevated permissions through membership
- Continuous Monitoring and Response: Implement detection rules for:
- Unusual role assignments or modifications
- Application credential additions (especially to privileged apps)
- Sign-ins from unusual locations or devices for privileged roles
- Privilege escalation via RBAC role assignments
- Guest account privilege elevation
The Hidden Escalation Path: Application Administrator Case Study
Let's examine a real-world attack scenario that demonstrates why role classification matters:
Initial Compromise: Attacker compromises an account with the Application Administrator role through password spraying attack.
Reconnaissance: Attacker enumerates all enterprise applications and service principals in the tenant, identifying one named "Azure Management" with:
- Admin Consent granted for RoleManagement.ReadWrite.Directory API permission
- Direct assignment to the Global Administrator role
Escalation: Attacker uses Application Administrator permissions to add a new client secret to the "Azure Management" service principal.
Pivot: Attacker authenticates as the service principal using the new secret, inheriting its Global Administrator role and full tenant control.
Lateral Movement: With Global Administrator, attacker grants themselves User Access Administrator at Azure Root Management Group, gaining control over all Azure subscriptions and infrastructure.
Persistence: Attacker creates multiple hidden service principals with privileged permissions and long-lived secrets, establishes backdoor conditional access exemptions, and registers malicious devices to the tenant.
Impact: Full tenant compromise, complete access to all M365 data (email, files, Teams), control over all Azure infrastructure, ability to exfiltrate data or deploy ransomware.
Detection: Without proper monitoring of Application Administrator activities and application credential modifications, this attack could remain undetected for months.
This scenario—which could be executed in under an hour by a moderately skilled attacker—demonstrates why the Application Administrator role must be classified as Medium-Risk despite its seemingly limited scope.
Practical Detection and Response
Critical Monitoring Points
Organizations should implement detection and alerting for these high-risk activities:
Entra ID:
- Any role assignment changes, especially for high-privilege roles
- Application credential additions or modifications
- Conditional Access policy changes
- Authentication policy modifications
- Federation settings changes
- Domain additions
- Privileged role activations from unusual locations or devices
- Guest account privilege escalations
Azure:
- Role assignments at Management Group or Subscription scope
- User Access Administrator role assignments
- Key Vault access policy modifications
- Managed Identity assignments to compute resources
- Network security group rule changes affecting administrative access
- Storage account key regenerations
- Secret or credential accesses from unexpected sources
Response Playbooks
Suspected High-Risk Role Compromise:
- Immediately revoke all active sessions for the compromised identity
- Reset credentials and invalidate all refresh tokens
- Review all recent activity for the compromised account
- Check for unauthorized role assignments, application registrations, or credential additions
- Hunt for persistence mechanisms (new admin accounts, backdoor applications, conditional access exemptions)
- Engage incident response procedures and preserve evidence
Unauthorized Privilege Escalation:
- Identify the escalation path (RBAC role assignment, application permissions, group membership)
- Immediately remove the unauthorized privilege
- Audit all activities performed with elevated privileges
- Identify and remediate the vulnerability that enabled escalation
- Review all identities with similar permissions for potential compromise
Beyond the Framework: Essential Complementary Controls
The risk-based privilege framework provides the foundation, but comprehensive cloud identity security requires additional layers:
1. Conditional Access Policies
- Block legacy authentication protocols globally
- Require compliant devices for privileged access
- Implement location-based restrictions for high-risk roles
- Block countries where you don't operate
- Enforce session controls (sign-in frequency, persistent browser sessions)
2. Identity Protection
- Enable Entra ID Identity Protection with automatic risk remediation
- Configure user risk policies to require password changes
- Configure sign-in risk policies to require MFA or block access
- Enable anonymous IP address detection
- Implement leaked credentials detection
3. Privileged Identity Management (PIM)
- Eliminate standing privileges for all high-risk and medium-risk roles
- Require approval workflows for role activation
- Enforce MFA on activation
- Limit activation duration (1-4 hours for high-risk, 1-8 hours for medium-risk)
- Configure audit and alerting for all activations
4. Break-Glass Accounts
- Maintain 2-3 cloud-only emergency access accounts
- Exclude from Conditional Access policies (but monitor heavily)
- Use strong passphrases stored in physical secure locations
- Configure high-priority alerts for any usage
- Review quarterly and test annually
5. Security Information and Event Management (SIEM)
- Centralize Entra ID and Azure logs in SIEM platform
- Implement threat detection rules for privilege escalation
- Correlate identity events with other security signals
- Retain logs for compliance and forensic analysis (minimum 90 days, ideally 1 year)
Common Implementation Challenges and Solutions
Challenge 1: "We can't afford dedicated PAWs for every admin"
Solution: Start with High-Risk roles only. A small organization might have 2-5 Global Administrators—even at $1,500 per PAW, that's $7,500 to protect accounts that control millions of dollars in cloud infrastructure and sensitive data. For Medium-Risk roles, virtual SAWs via Azure Virtual Desktop provide similar isolation at lower cost.
Alternative: Implement strict device compliance requirements and app protection policies as an interim control while budgeting for dedicated hardware.
Challenge 2: "Just-in-time access will slow down incident response"
Solution: Configure appropriate maximum activation durations (up to 4 hours for high-risk, 8 hours for medium-risk) and implement streamlined approval workflows. For true emergencies, maintain properly secured break-glass accounts. Most "emergencies" requiring immediate Global Administrator access aren't actually emergencies—they're planning failures.
Challenge 3: "Cloud-only accounts complicate our identity management"
Solution: This is a feature, not a bug. Cloud-only privileged accounts provide critical isolation from on-premises compromise. Implement a clear naming convention (e.g., admin_firstname.lastname@company.com), document them centrally, and manage them via Azure AD administrative units for governance.
Challenge 4: "We have hundreds of Azure subscriptions—how do we classify them all?"
Solution: Start with clear classification criteria (production vs. non-production, data sensitivity, compliance scope, business criticality). Work with business units to classify subscriptions, then apply role restrictions based on classification. Use Azure Policy to enforce role assignment restrictions at the Management Group level.
Challenge 5: "Service principals with Managed Identities don't work for our CI/CD pipeline"
Solution: Use Workload Identity Federation to eliminate long-lived secrets while maintaining automated workflows. Azure DevOps, GitHub Actions, and GitLab all support federated credentials that enable CI/CD pipelines to authenticate without storing secrets. This is more secure and eliminates secret rotation burden.
Measuring Success: Key Metrics
Organizations should track these metrics to measure framework implementation and ongoing effectiveness:
Implementation Metrics:
- Percentage of high-risk role assignments meeting all security controls
- Percentage of medium-risk role assignments meeting all security controls
- Percentage of machine identities using Managed or Federated Identities (target: 90%+)
- Average time to provision just-in-time privileged access
- Number of standing privilege assignments eliminated
Security Metrics:
- Number of privileged role assignments (trend should decrease)
- Percentage of privileged accounts with phishing-resistant MFA (target: 100% for high/medium-risk)
- Mean time to detect (MTTD) privileged account compromise
- Mean time to respond (MTTR) to privilege escalation incidents
- Number of hidden privilege escalation paths discovered and remediated
Operational Metrics:
- Just-in-time access request approval time
- Privileged access session durations (should align with policy)
- Number of emergency access account activations (should be rare)
- Administrative overhead (should stabilize after initial implementation)
The Cloud Identity Security Reality
The convergence of Microsoft Entra ID and Azure creates an attack surface that most organizations don't fully understand. Default over-privileging, hidden escalation paths, and inefficient security controls leave the "keys to the kingdom" vulnerable to compromise.
CVE-2025-55241 demonstrated that even Microsoft's most fundamental identity infrastructure can harbor critical vulnerabilities. But most organizations won't be compromised by sophisticated zero-day exploits—they'll be breached through misconfigured permissions, compromised privileged accounts without MFA, or service principals with excessive rights and leaked credentials.
The risk-based privilege framework provides a structured approach to focus your most robust security controls on the roles that pose the greatest risk. By moving beyond one-size-fits-all security postures, organizations can:
- Reduce attack surface by eliminating standing privileges and restricting high-risk role access
- Accelerate detection by focusing monitoring resources on highest-impact activities
- Improve resilience by implementing defense-in-depth controls proportionate to risk
- Enable efficiency by not over-securing low-risk roles while under-securing critical ones
This isn't a security project with a defined end date—it's a foundational component of continuous cloud security operations. The cloud identity landscape constantly evolves: new roles are added, permissions change, and attack techniques advance. Regular reassessment and adjustment of security controls is essential.
Take Action: Your Next Steps
- Download and review the full whitepaper: "Securing Identities in the Microsoft Cloud" (link: https://security.googlecloudcommunity.com/community-blog-42/whitepaper-securing-identities-in-the-microsoft-cloud-6077)
- Assess your current state: Inventory all high-risk and medium-risk role assignments in your Entra ID tenant and Azure subscriptions. How many meet the framework's security requirements?
- Prioritize quick wins: Implement phishing-resistant MFA for all Global Administrators today. Enable Privileged Identity Management and eliminate standing Global Administrator assignments this week.
- Build your roadmap: Create a phased implementation plan starting with high-risk roles, then medium-risk, then low-risk. Assign ownership, allocate resources, and set realistic timelines.
- Establish continuous monitoring: Implement detection rules for privilege escalation and administrative account compromise. Review privileged access logs weekly.
- Test your defenses: Conduct regular privileged access reviews. Simulate compromise scenarios. Test break-glass account procedures annually.
- Stay informed: Subscribe to Microsoft security advisories, follow cloud security researchers, and participate in the security community. The threat landscape evolves rapidly—your defenses must evolve with it.
The Bottom Line: In the cloud, identity is the perimeter. Every privileged account is a potential path to total compromise. The question isn't whether attackers will attempt to exploit your cloud identities—it's whether your security controls are strong enough to stop them. A risk-based privilege framework ensures you're focusing your strongest defenses where they matter most: protecting the keys to your cloud kingdom.
This article is based on the whitepaper "Securing Identities in the Microsoft Cloud" by Razvan Buliga and Ischa Rijff, published by the Google Cloud Community. For more detailed technical guidance, implementation specifics, and complete role classification tables, download the full whitepaper.
About CISO Marketplace: We provide offensive security services, vCISO consulting, and compliance assessments to help organizations secure their cloud infrastructure and meet regulatory requirements. Our extensive ecosystem includes specialized resources at breached.company, compliancehub.wiki, and microsec.tools. For comprehensive cloud identity security assessments or implementation guidance for the risk-based privilege framework, contact us at [contact information].
Tags: #MicrosoftEntraID #AzureSecurity #CloudSecurity #IdentityManagement #PrivilegeEscalation #ZeroTrust #RBAC #CloudCompliance #CyberSecurity #ThreatDetection #IncidentResponse #vCISO






