WhatsApp Under Siege: How 'Maverick' Malware Is Hijacking Brazilian Banking Accounts

Executive Summary
A sophisticated malware campaign dubbed "Water Saci" is leveraging WhatsApp's massive user base in Brazil to deploy banking trojans that hijack browser sessions and steal financial credentials. With 148 million WhatsApp users in Brazil representing 98% of smartphone users with the messaging app, cybercriminals have found the perfect vector for mass-scale propagation. The campaign combines two primary malware components—SORVEPOTEL and Maverick—that work in tandem to compromise WhatsApp Web sessions, disable security software, and target over 65 Latin American financial institutions.
The Perfect Storm: Why Brazil?
Brazil represents the second-largest WhatsApp market globally, creating an ideal environment for social engineering attacks. The campaign has concentrated heavily in Brazil, accounting for 457 of 477 recorded infections, with most victims in government and public service sectors, though manufacturing, education, banking, technology, and construction sectors have also been affected.
The country's cybersecurity landscape is uniquely challenging. Brazilian Portuguese-specific cybercriminal communities enable a localized domestic threat, with actors relying significantly on mobile apps and social media platforms like Telegram and WhatsApp rather than traditional underground forums. This ecosystem has fostered a mentoring culture where experienced threat actors teach new members, accelerating the sophistication of attacks.
The Attack Architecture: A Two-Pronged Assault
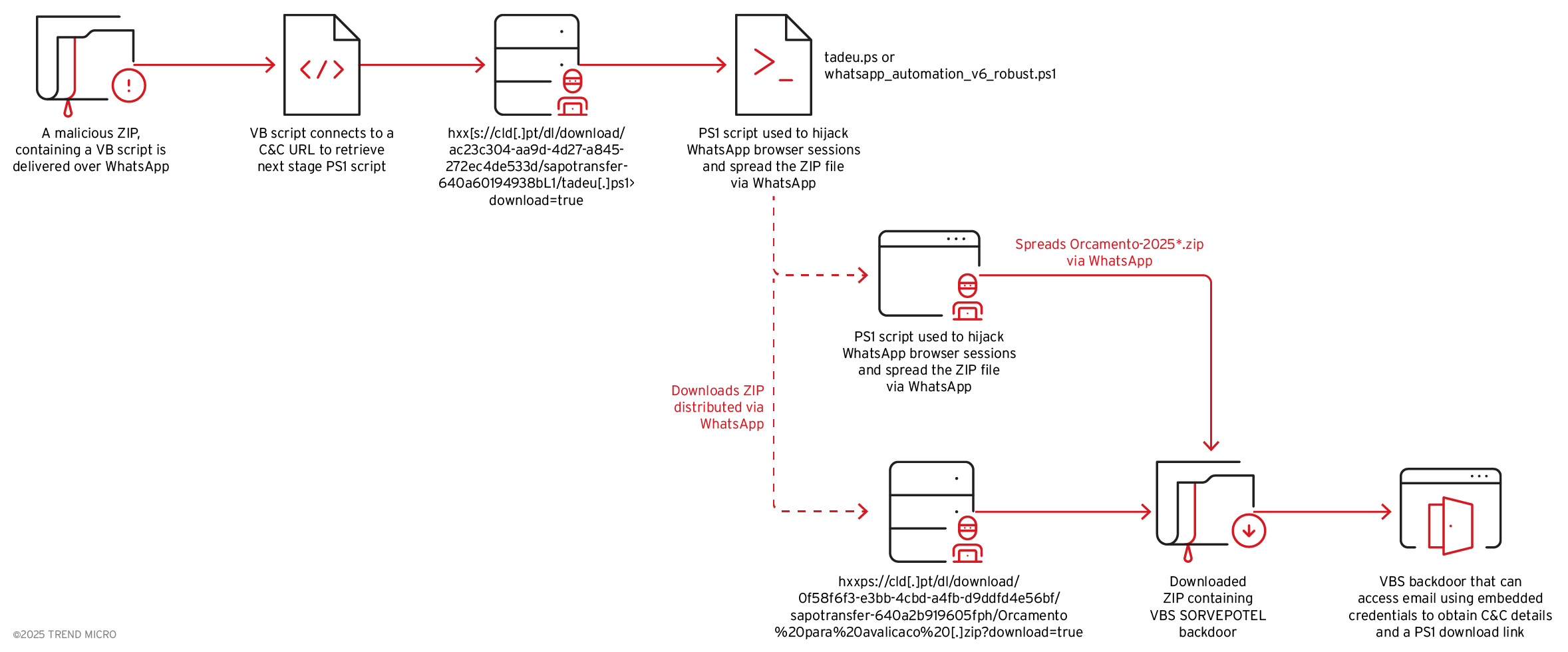
Component 1: SORVEPOTEL - The Self-Propagating Worm
SORVEPOTEL is a self-propagating malware spread via the desktop web version of WhatsApp and is used to deliver a ZIP archive containing the Maverick payload. The worm's propagation mechanism is particularly insidious:
Initial Infection Vector:
- Victims receive WhatsApp messages from compromised contacts—typically friends or colleagues
- Messages contain ZIP archives disguised as legitimate documents (receipts, health forms, quotations)
- File names follow patterns like "Orcamento-2025[8 random digits].zip"
- Alternative distribution: There is evidence that operators have also used emails to distribute ZIP files from seemingly legitimate email addresses, expanding the attack surface beyond WhatsApp alone
WhatsApp Web Hijacking: The malware terminates existing Chrome processes and clears old sessions before copying the victim's legitimate Chrome profile data to its temporary workspace, including cookies, authentication tokens, and saved browser sessions. This technique bypasses WhatsApp Web's authentication entirely, gaining immediate access without triggering security alerts or requiring QR code scanning.

The automation is sophisticated, leveraging browser automation tools like Selenium to control WhatsApp Web and programmatically send messages. The script displays a deceptive banner labeled "WhatsApp Automation v6.0" to hide its ongoing operations activity, retrieves message templates from a command-and-control server, and exfiltrates the victim's contact list. The malware then iterates through every harvested contact, checks for pause commands, and sends personalized messages by substituting variables with time-based greetings and contact names.
Component 2: Maverick - The Banking Trojan
Maverick represents the payload component focused on financial credential theft. The malware checks active browser window URLs against a hard-coded list of 65 financial institutions in Latin America, particularly those located in Brazil. When a match is detected, Maverick invokes its Agent component to establish communication with command-and-control servers.
Geographic Targeting: Maverick is only installed after ensuring that the victim is located in Brazil by checking the time zone, language, region, and date and time format of the infected host. This precision targeting reduces detection risks and focuses resources on high-value targets.
Banking Targets: The malware specifically targets some of Brazil's largest financial institutions and payment platforms, including:
- Banco do Brasil
- Bradesco
- Caixa Econômica Federal (CEF)
- Itaú Unibanco
- Banco do Nordeste
- Santander
- Sicredi
- Mercado Pago
- Binance (cryptocurrency exchange)
Expanding Scope: CyberProof found evidence of the malware being used to single out hotels in Brazil, indicating a possible expansion of targeting, suggesting the threat actors are diversifying beyond traditional banking targets.
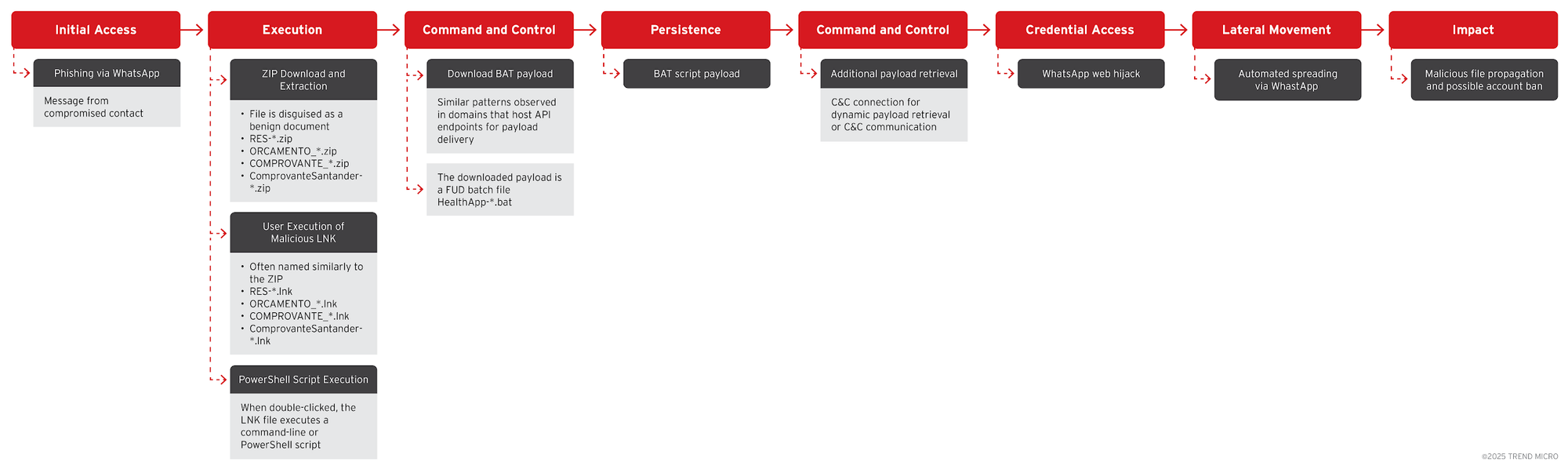
Technical Deep Dive: The Infection Chain
Stage 1: Initial Compromise
The infection begins when a user downloads and extracts a malicious ZIP archive from WhatsApp. The ZIP file contains a Windows shortcut (LNK) that, when launched, runs cmd.exe or PowerShell to connect to an external server to download the first-stage payload.
The PowerShell script is designed to:
- Launch intermediate tools to disable Microsoft Defender Antivirus and UAC
- Retrieve a .NET loader with anti-analysis capabilities
- Check for presence of reverse engineering tools and self-terminate if detected

Stage 2: Payload Deployment
The .NET DLL binary reaches out to an external server to fetch Maverick.StageTwo and a downloader DLL associated with hijacking WhatsApp Web that runs only on systems with an active, logged-in WhatsApp session.
Before fetching payloads, the DLL implements anti-analysis checks by scanning for debugging tools including apimonitor, blurp, fiddler, ghidra, IDA, windbg, wireshark, and x64debug.
Stage 3: Command and Control
The campaign features an innovative C2 infrastructure. SORVEPOTEL leverages IMAP connections to terra.com[.]br email accounts using hardcoded email credentials to retrieve commands rather than using traditional HTTP-based communication. Some of these accounts have been secured using multi-factor authentication to prevent unauthorized access by security researchers.
Supported Backdoor Commands
The backdoor periodically polls the C2 server for instructions, supporting 22 different commands including:
Information Gathering:
- INFO: Collect detailed system information
- SCREENSHOT: Take screenshots
- TASKLIST: Enumerate running processes
- FILE_INFO: Get detailed metadata about files
- Keylogging: Log keystrokes to capture credentials and sensitive information
- Application enumeration: Gather list of installed applications
System Manipulation:
- CMD/POWERSHELL: Execute commands
- KILL: Terminate specific processes
- REBOOT/SHUTDOWN: System restart or shutdown with 30-second delay
- Inject characters: Insert one or more characters into the system
- Create overlay screens: Block keyboard and mouse interactions to prevent user control
Credential Theft:
- Serve fake banking security alerts
- Display phishing pages mimicking legitimate financial websites
- Steal authentication tokens and user credentials
File Operations:
- LIST_FILES: Enumerate files/folders
- DOWNLOAD_FILE/UPLOAD_FILE: Transfer files
- DELETE/RENAME/COPY/MOVE: File system manipulation
- CREATE_FOLDER: Directory creation
- SEARCH: Recursively search for files
Malware Management:
- UPDATE: Download and install updated versions
- CHECK_EMAIL: Check attacker-controlled email for new C2 URLs
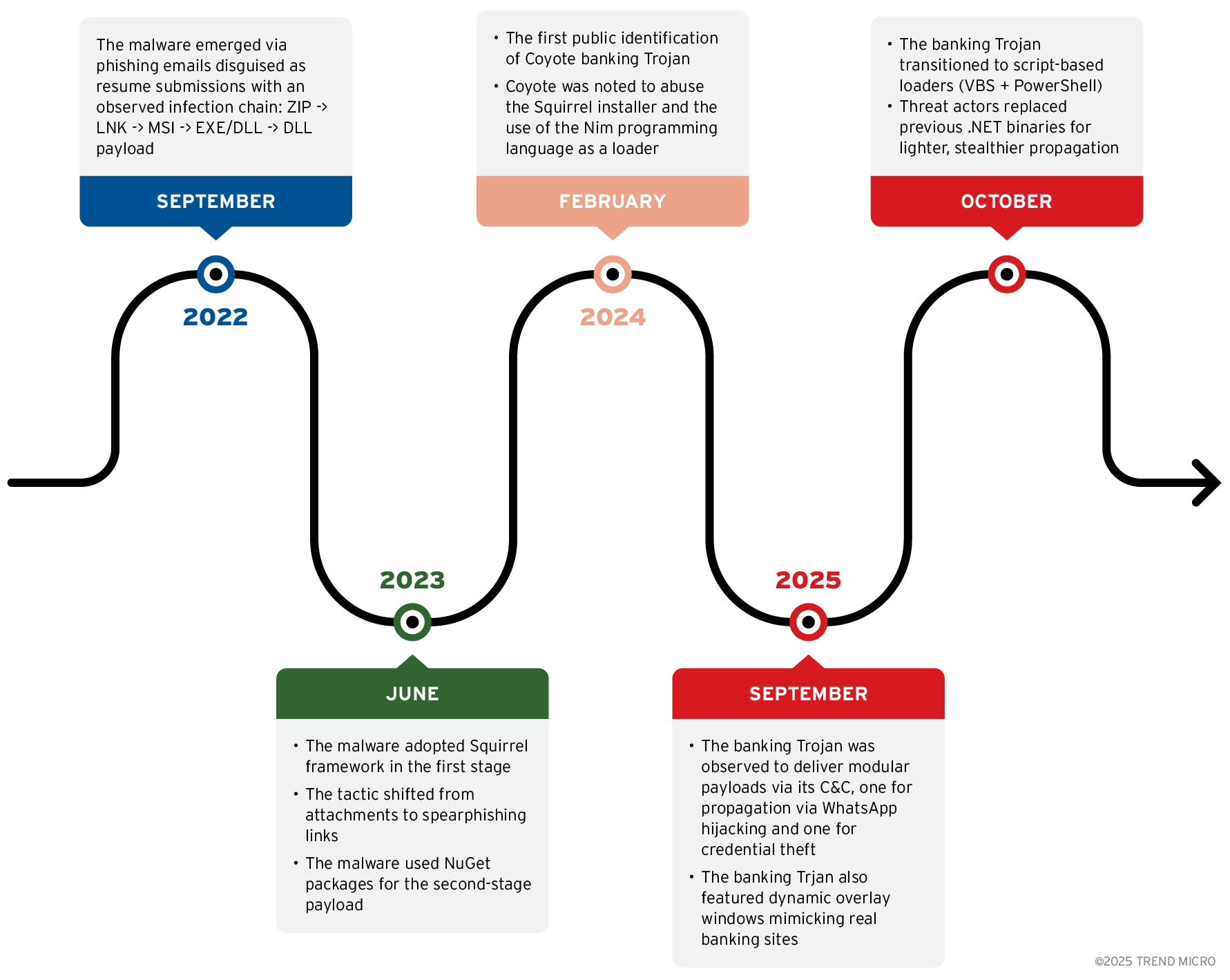
The Evolution: From Coyote to Maverick
The cybersecurity community has identified significant overlaps between Maverick and an earlier banking trojan called Coyote. According to a report from CyberProof, both malware strains are written in .NET, target Brazilian users and banks, and feature identical functionality to decrypt, targeting banking URLs and monitor banking applications.
However, Kaspersky found that Maverick did contain many code overlaps with Coyote, but the Russian cybersecurity company noted it's treating it as a completely new threat targeting Brazil en masse. This suggests either an evolution of the same threat group or parallel development within Brazil's cybercriminal ecosystem.
Trend Micro said that the infection methods and ongoing tactical evolution, along with the region-focused targeting, indicate that Water Saci is likely linked to Coyote, and both campaigns operate within the same Brazilian cybercriminal ecosystem, describing the attackers as aggressive in "quantity and quality."
Real-Time Botnet Management
One of the most concerning aspects of this campaign is the level of control threat actors maintain over infected systems. The new attack chain features a sophisticated remote command-and-control system that allows threat actors real-time management, including pausing, resuming, and monitoring the malware's campaign, effectively converting infected machines into a botnet tool for coordinated, dynamic operations across multiple endpoints.
This capability allows attackers to:
- Coordinate mass-distribution campaigns
- Pause operations to avoid detection during security investigations
- Resume attacks when security focus shifts elsewhere
- Monitor infection rates and adjust tactics in real-time
Related Campaigns: Eternidade Stealer and Astaroth
The WhatsApp malware ecosystem in Brazil extends beyond Maverick. Another banking trojan called Eternidade Stealer has been spreading through WhatsApp since early 2025, specifically targeting crypto wallets and financial logins. The malware hunts for credentials from exchanges including Binance, Coinbase, and Kraken, as well as popular crypto wallets like MetaMask, Trust Wallet, and Exodus.
Sophos analysts are investigating a separate campaign tracked as STAC3150, first observed on September 24, 2025, which delivers archive attachments containing a downloader script that retrieves multiple second-stage payloads including the Astaroth banking trojan. This campaign has affected more than 250 Sophos customers, with approximately 95% of impacted devices located in Brazil.

Detection and Prevention Strategies
For Organizations
1. Endpoint Protection:
- Deploy advanced EDR solutions capable of detecting in-memory execution
- Monitor for PowerShell execution with Base64-encoded commands
- Implement application whitelisting to prevent unauthorized executables
2. Network Security:
- Monitor for unusual IMAP connections to terra.com[.]br email accounts
- Block connections to known malicious domains (zapgrande[.]com, adoblesecuryt[.]com)
- Implement DNS filtering to prevent C2 communications
3. Email and Messaging Policy:
- Disable automatic downloads on WhatsApp Web for corporate devices
- Restrict file transfers through WhatsApp and similar apps on organizational devices
- Implement Mobile Device Management policies enforcing app store-only downloads
4. User Education:
- Train employees to be suspicious of ZIP files received via WhatsApp, even from known contacts
- Establish verification procedures for unexpected file transfers
- Encourage users to log out of messaging apps when not in use
For Individuals
1. Behavioral Security:
- Never open ZIP attachments from WhatsApp without verifying through a different channel
- Be especially wary of messages about government programs, delivery notifications, or investment opportunities
- Verify unexpected requests from contacts before clicking links or downloading files
2. System Hardening:
- Keep Windows, browsers, and security software updated
- Enable Microsoft Defender Antivirus and ensure it's not disabled
- Install reputable endpoint security software with real-time protection
3. Session Management:
- Regularly clear browser cookies and authentication tokens
- Log out of WhatsApp Web when not actively using it
- Use separate browsers for financial transactions and general browsing

The Broader Implications
The Water Saci campaign represents a significant evolution in banking malware distribution. Threat actors have transitioned from relying on traditional payloads to exploiting legitimate browser profiles and messaging platforms for stealthy, scalable attacks.
Several factors make this campaign particularly concerning:
1. Scale of Impact: With 148 million potential targets in Brazil alone, the attack surface is enormous. WhatsApp's position as the dominant communication platform means nearly every Brazilian with a smartphone is potentially vulnerable.
2. Trust Exploitation: The use of compromised contacts' accounts to distribute malware exploits fundamental trust relationships. Users are conditioned to trust messages from known contacts, making this vector highly effective.
3. Technical Sophistication: The multi-stage attack chain, email-based C2, browser automation, and real-time botnet management demonstrate advanced capabilities typically associated with nation-state actors.
4. Economic Motivation: Brazil's significant cryptocurrency adoption—ranking fifth globally on the Chainalysis crypto adoption index with approximately $319 billion in transactions between mid-2024 and mid-2025—makes it an attractive target for financially motivated threat actors.
Looking Forward: The Threat Landscape
The success of the Water Saci campaign is likely to inspire similar attacks in other regions with high WhatsApp adoption. Key indicators to watch include:
1. Geographic Expansion: While currently focused on Brazil, the techniques could easily be adapted for other Latin American countries or any region with high WhatsApp usage.
2. Platform Diversification: The core techniques of browser session hijacking and messaging app exploitation could be adapted for other platforms like Telegram, Signal, or regional messaging apps.
3. Increased Sophistication: The mentoring culture in Brazil's cybercriminal ecosystem means continuous knowledge transfer and capability enhancement among threat actors.
4. Commercial Malware-as-a-Service: The modular nature of SORVEPOTEL and Maverick suggests potential for commercialization, where components could be sold or rented to other threat actors.

Recommendations for Security Leaders
Immediate Actions:
- Audit corporate policies regarding WhatsApp Web usage
- Deploy detection rules for the specific TTPs used in this campaign
- Conduct targeted user awareness training on WhatsApp-based threats
- Review and strengthen endpoint security configurations
Medium-Term Initiatives:
- Implement Zero Trust architecture that doesn't rely on device trust alone
- Deploy behavioral analytics to detect session hijacking attempts
- Establish cross-functional incident response procedures for messaging app compromises
- Partner with regional CERTs and ISACs for threat intelligence sharing
Long-Term Strategy:
- Evaluate business necessity of allowing personal messaging apps on corporate devices
- Consider implementing separate mobile devices for work and personal use
- Invest in advanced threat hunting capabilities focused on fileless malware
- Develop comprehensive security awareness programs that address evolving social engineering tactics
Related Resources from CISO Marketplace Network
To better understand the broader context of WhatsApp and Meta security concerns, explore these additional resources from our network:
Privacy and Security Guides
- The Complete Guide to Social Media Privacy: Protecting Your Digital Life in 2025 - Comprehensive coverage of privacy settings across all major platforms including WhatsApp
- Meta AI's Privacy Controversy: Instagram and Beyond - Understanding how Meta integrates AI across WhatsApp, Instagram, and Facebook
- Facebook Security Essentials: A 2025 Technical Guide - Technical security strategies for Meta platforms
Understanding Meta's Data Practices
- The Privacy Implications of Meta AI: User Data and AI Integration Across Platforms - How data sharing across WhatsApp, Instagram, Messenger, and Facebook creates security risks
- A Comprehensive Guide to Facebook/Meta Privacy Settings - Step-by-step privacy configuration for Meta platforms
For compliance professionals, additional regulatory guidance on secure messaging and data protection is available at ComplianceHub.wiki, and for breach notifications and incident reports, visit Breached.company.
Conclusion
The Maverick and SORVEPOTEL malware campaign demonstrates how threat actors are increasingly exploiting trusted communication platforms to achieve mass-scale compromise. Brazil's unique position as WhatsApp's second-largest market, combined with a sophisticated domestic cybercriminal ecosystem, has created perfect conditions for this campaign to thrive.
For security professionals, this campaign serves as a stark reminder that traditional security controls may be insufficient against attacks that exploit legitimate browser profiles, trusted communication platforms, and social engineering at scale. The key to defense lies in a multi-layered approach combining technical controls, user education, and continuous threat intelligence monitoring.
As Trend Micro described the attackers as aggressive in "quantity and quality," organizations must remain vigilant and proactive in their defense strategies. The sophistication demonstrated by the Water Saci campaign suggests we're witnessing not just an isolated attack, but a fundamental shift in how financial malware is distributed and operated in the mobile-first era.
Indicators of Compromise (IoCs)
Command and Control Servers:
- zapgrande[.]com
- sorvetenopoate[.]com
- adoblesecuryt[.]com
- terra.com[.]br (IMAP-based C2)
File Indicators:
- ZIP files following pattern: Orcamento-2025[8 random digits].zip
- VBS files: Orcamento.vbs (SORVEPOTEL)
- PowerShell scripts: tadeu.ps1
- Malicious LNK shortcuts in ZIP archives
- .NET DLL: Maverick.StageTwo
- Maverick.Agent component
- WinManagers.vbs in C:\ProgramData\WindowsManager\
Behavioral Indicators:
- Unexpected Chrome process terminations followed by restarts
- PowerShell execution with Base64-encoded commands
- IMAP connections to terra.com[.]br
- Mass-messaging behavior from WhatsApp Web sessions
- Disabled Microsoft Defender Antivirus or UAC
- Unusual browser automation using ChromeDriver and Selenium
- Reflective DLL loading in memory
- Code injection into powershell_ise.exe
Network Indicators:
- Connections to Portuguese-named URLs
- HTTPS traffic to uncommon .br domains
- Elevated WhatsApp Web session activity
- File downloads from external servers via PowerShell
- Selenium WebDriver traffic patterns
References: This article synthesizes intelligence from Trend Micro, CyberProof, Kaspersky, Sophos, Google Cloud Threat Intelligence, and independent security researchers tracking the Water Saci campaign.










